Secure Socket Layer Yu Yang Lilly Wang 1
51 Slides1,003.00 KB
Secure Socket Layer Yu Yang Lilly Wang 1
Agenda SSL Basics WTLS Security for Web Service 2
SSL Facts SSL was first developed by Netscape in 1994 and became an internet standard in 1996 ( RFC 2246 – TLS V1.0) SSL is a cryptographic protocol to secure network across a connection-oriented layer Any program using TCP can be modified to use SSL connection 3
SSL Facts SSL connection uses a dedicated TCP/IP socket(e.g. port 443 for https) SSL is flexible in choice of which symmetric encryption, message digest, and authentication can be used SSL provides built in data compression 4
SSL Usage Authenticate the server to the client Allow the client and server to select cryptographic algorithms, or ciphers, that they both support Optionally authenticate the client to the server Use public key encryption techniques to generate shared secret Establish an encrypted SSL connection 5
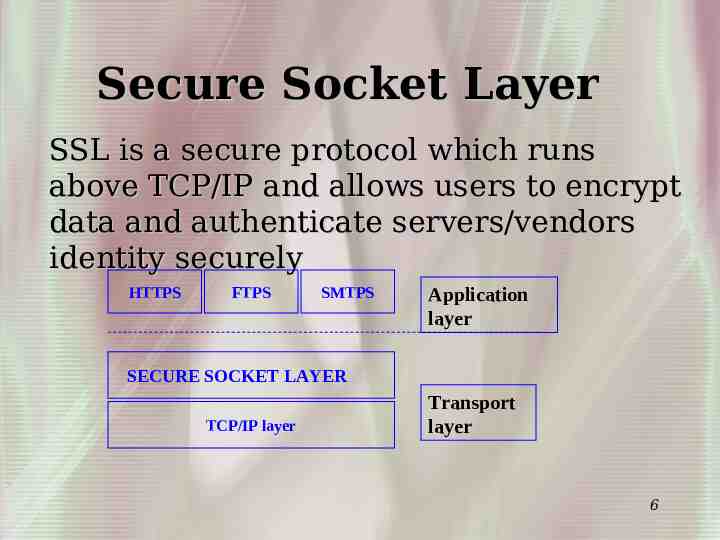
Secure Socket Layer SSL is a secure protocol which runs above TCP/IP and allows users to encrypt data and authenticate servers/vendors identity securely HTTPS FTPS SMTPS Application layer SECURE SOCKET LAYER TCP/IP layer Transport layer 6
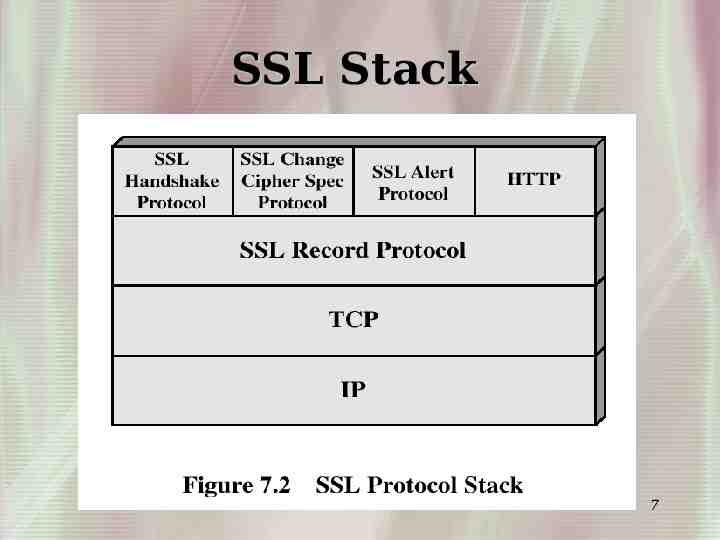
SSL Stack 7
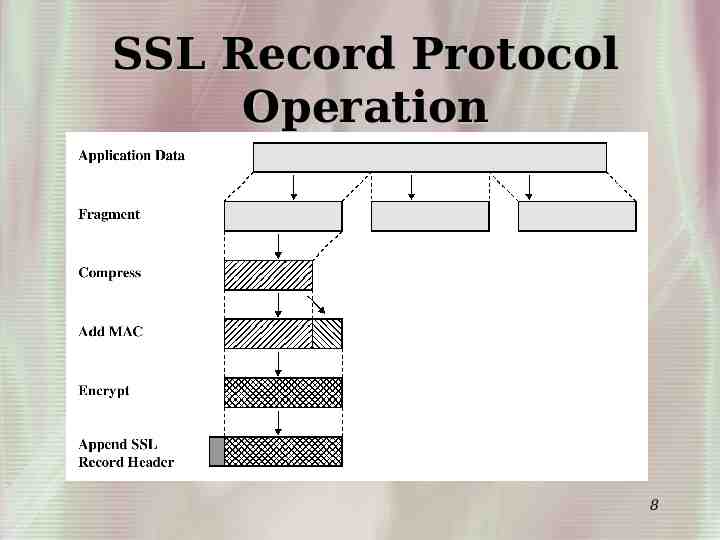
SSL Record Protocol Operation 8
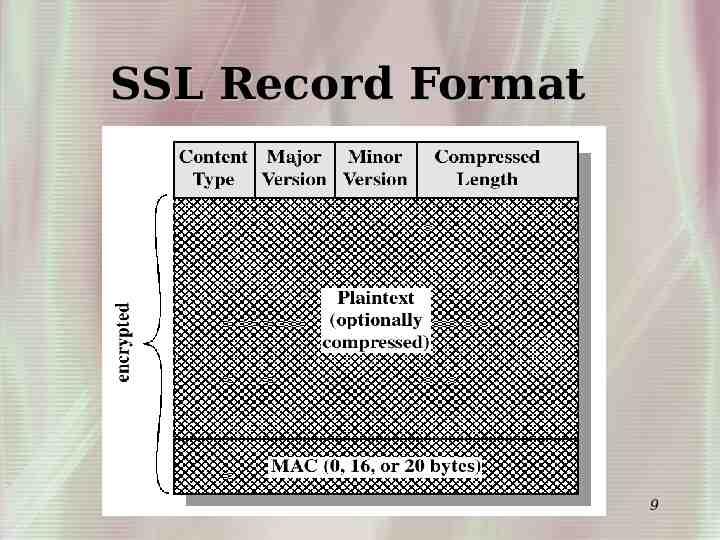
SSL Record Format 9
SSL Handshake SSL handshake verifies the server and allows client and server to agree on an encryption set before any data is sent out 10
SSL Handshake 11
SSL Handshake Server Public key Private key Client request Client Public key 12
SSL Session Key Server Private key Public key PreMaster Session key PreMaster Client Public key Pre-Master Session key 13
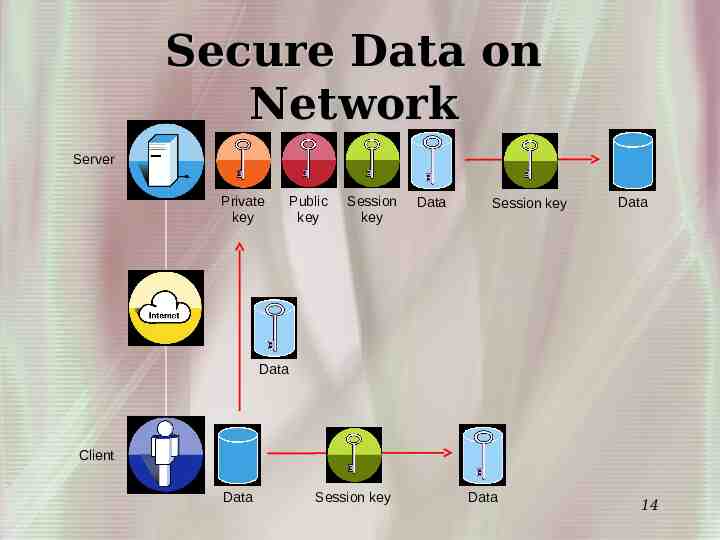
Secure Data on Network Server Private key Public key Session key Data Session key Data Data Client Data Session key Data 14
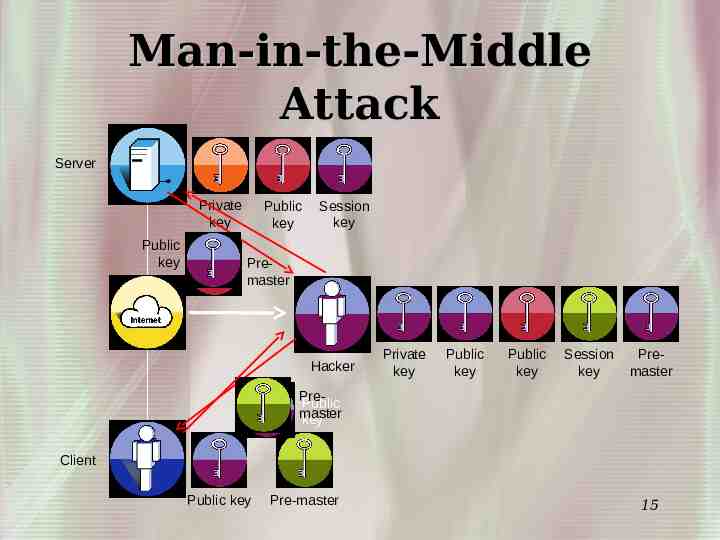
Man-in-the-Middle Attack Server Private key Public key Public key Session key Premaster Hacker Private key Public key Public key Session key Premaster PrePublic master key Client Public key Pre-master 15
Key exchange and certificate Server Private key Public key SSL version number client supported (v2, v3) SSL version number server picked (v2, v3) Ciphers supported client (DES, RC2, RC4) Ciphers server picked (DES, RC2, RC4) Client Random Number Server Random Number Certificate Client Public key 16
Verify Certificate Server Private key Public key Certificate is Good and Valid Server/vendor has been verified and authenticated Client request Certificate Client has vendor’s public key and can now encrypt pre-master to send to server/vendor Valid Checking Client Public key Certificate 17
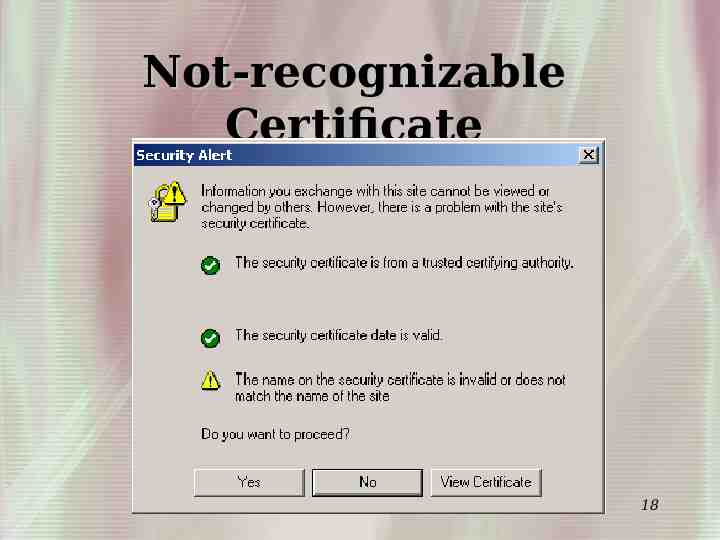
Not-recognizable Certificate 18
Review the Certificate In IE 19
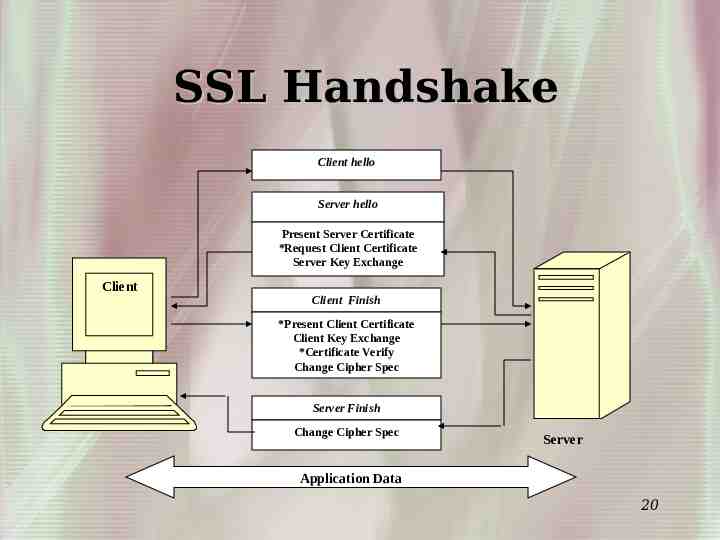
SSL Handshake Client hello Server hello Present Server Certificate *Request Client Certificate Server Key Exchange Client Client Finish *Present Client Certificate Client Key Exchange *Certificate Verify Change Cipher Spec Server Finish Change Cipher Spec Server Application Data 20
Server Hello Request Notifies the client that they should send a client hello message to begin the negotiation process Sent by the server at any time After the server sends a request, it does not send another one until a handshake has been completed Client can choose to ignore them or send a Client Hello 21
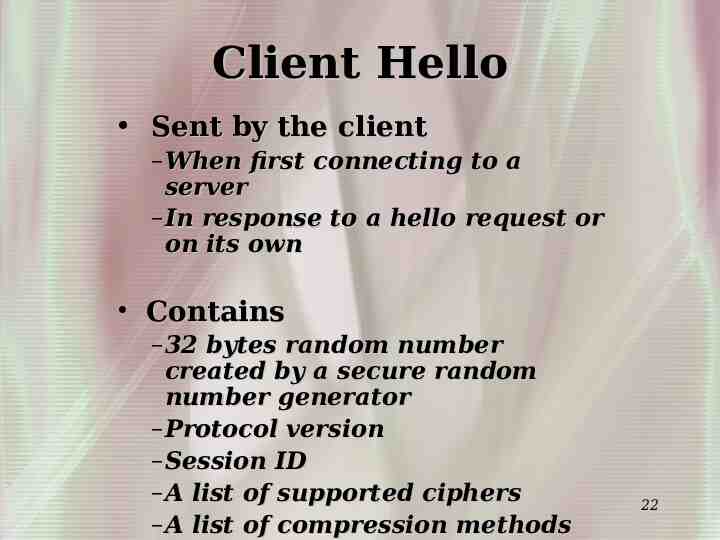
Client Hello Sent by the client – When first connecting to a server – In response to a hello request or on its own Contains – 32 bytes random number created by a secure random number generator – Protocol version – Session ID – A list of supported ciphers – A list of compression methods 22
Server Hello Sent as response if client hello is accepted – If not, a handshake failure alert is sent Contains – 32 bytes random number created by a secure random number generator – Protocol version – Session ID – Cipher suite chosen – Compression method selected 23
Server Certificates Immediately following the server hello, the server sends its certificate – Generally an X.509.v3 certificate Server sends server hello done message 24
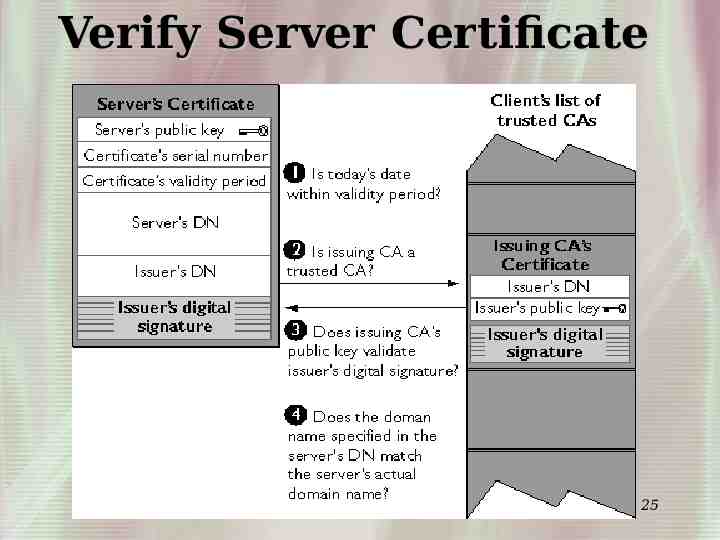
Verify Server Certificate 25
Client Certificate (optional) Client only sends a certificate upon the receipt of a certificate request – Sends after receiving server hello done – If the client does not have a suitable certificate, it sends a no certificate alert Server will respond with a fatal handshake failure if a client certificate is necessary 26
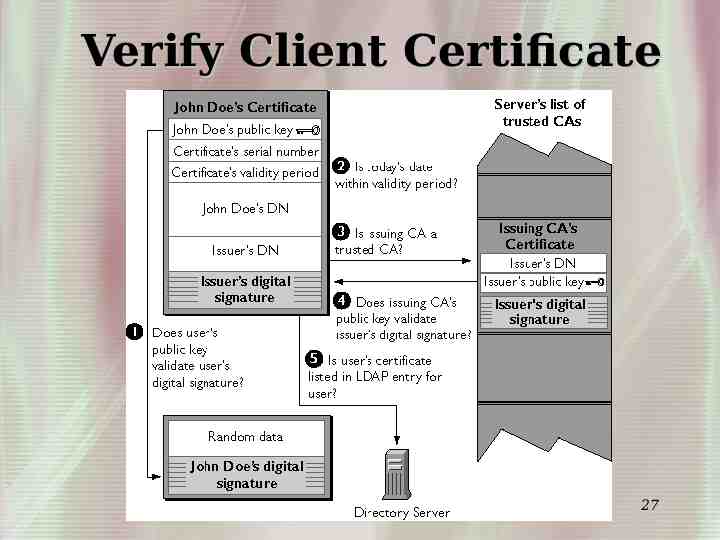
Verify Client Certificate 27
Key Exchange Client sends 48-bytes pre-master, encrypted using server’s public key, to the server Both server and client use the pre-master to generate the master secret A same session key is generated on both client and server side using the master secret 28
Final Steps Client sends change cipher spec Client sends finished message Server sends change cipher spec Server sends finished message 29
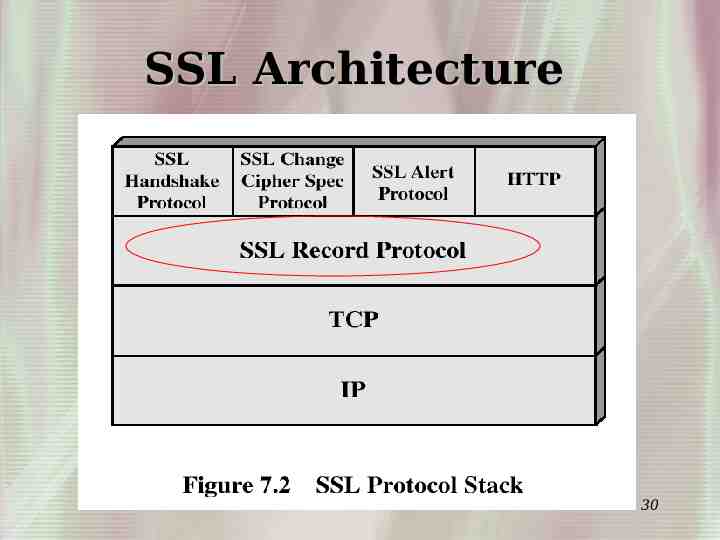
SSL Architecture 30
Record Layer Compression and decompression A MAC is applied to each record using the MAC algorithm defined in the current cipher spec Encryption occurs after compression May need fragmentation 31
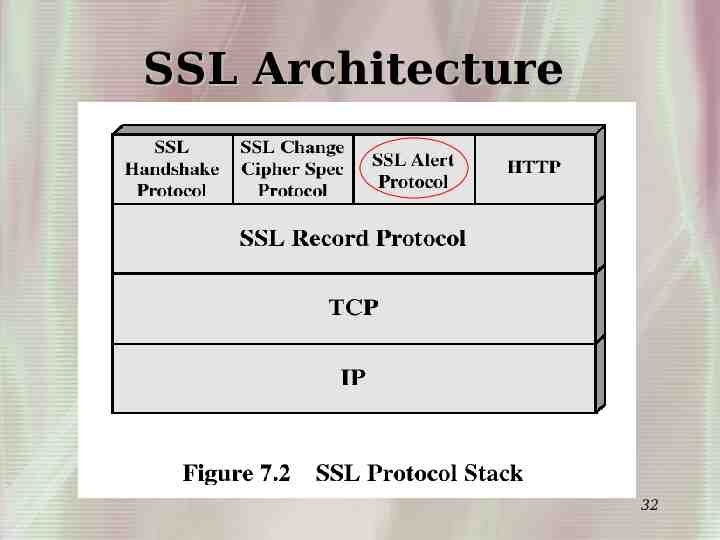
SSL Architecture 32
Alert Layer Explain severity of the message and a description –fatal Immediate termination Other connections in session may continue Session ID invalidated to prevent failed session to open new sessions Alerts are compressed same as other data 33
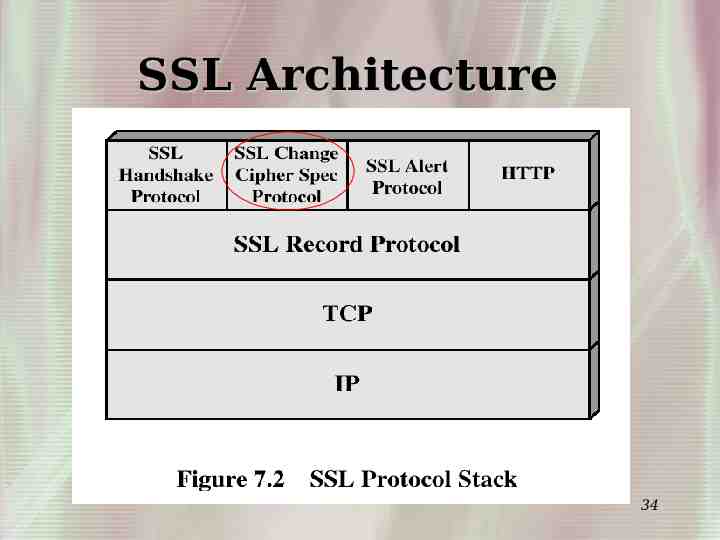
SSL Architecture 34
Change Cipher Spec Protocol Notify the other party to use the new cipher suite Before the Finished message 35
Comparison of SSL V2.0 and V3.0 SSL 2.0 is vulnerable to “manin-the-middle” attack. The hello message can be modified to use 40 bits encryption. SSL 3.0 defends against this attack by having the last handshake message include a hash of all the previous handshake message 36
Comparison of SSL V2.0 and V3.0 SSL 2.0 uses a weak MAC construction In SSL 3.0, the Message Authentication Hash uses a full 128 bits of key material for Export cipher, while SSL 2.0 uses only 40 bits 37
Comparison of SSL V2.0 and V3.0 SSL 2.0 only allows a handshake at the beginning of the connection. In 3.0, the client can initiate a handshake routine any time SSL 3.0 allows server and client to send chains of certificate SSL 3.0 has a generalized key exchange protocol. It allows Diffie-Hellman and Fortezza key exchange SSL 3.0 allows for record compression 38 and decompression
Problem Free? Side channel attack – discovered by Swiss Federal Institute of Technology in Lausanne http://www.newsfactor.com/perl/story/20843.html Information leak in encrypted connections. Vulnerable openssl versions do not perform a MAC computation if an incorrect block cipher padding is used. An active attacker who can insert data into an existing encrypted connection is then able to measure time differences between the error messages the server sends. This information can make it easier to launch cryptographic attacks that rely on 39 distinguishing between padding and MAC
Wireless Transport Layer Security 40
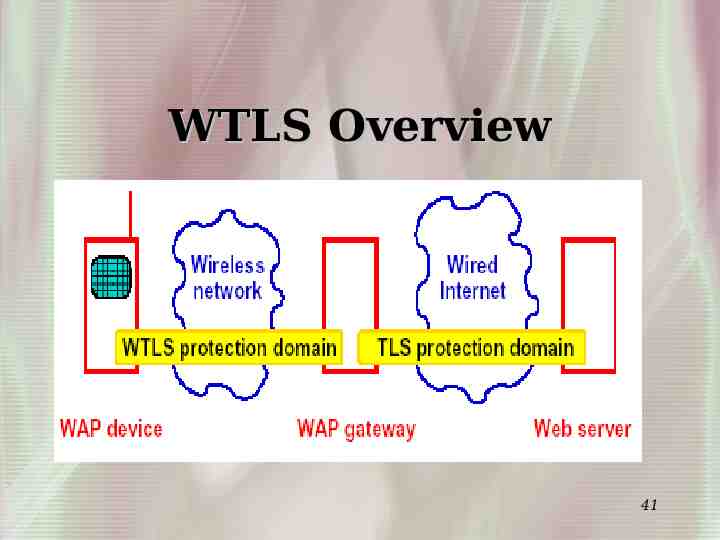
WTLS Overview 41
WTLS Facts Mainly used to secure data transport between wireless device and gateway Built on top of datagram (UDP) instead of TCP WTLS provides full, optimized and abbreviated handshake to reduce roundtrips in high-latency networks 42
WTLS Facts WTLS uses different format of certificates, mainly WTLS certificate, X509v1 and 968. It also supports additional cipher suites, such as RC5, short hashes, ECC, etc; WTLS provides built-in key-refresh mechanism for renegotiation; WTLS can also set session resumable to continue on a previous session. 43
Web Service Security 44
Comparison of Traditional Web Application and Web Service Client-server system vs multiparty Simple protocol sets vs complicated protocol sets 45
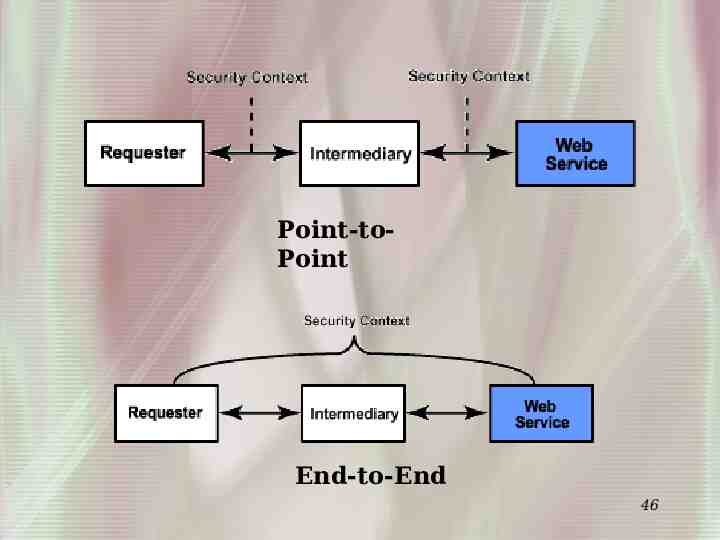
Point-toPoint End-to-End 46
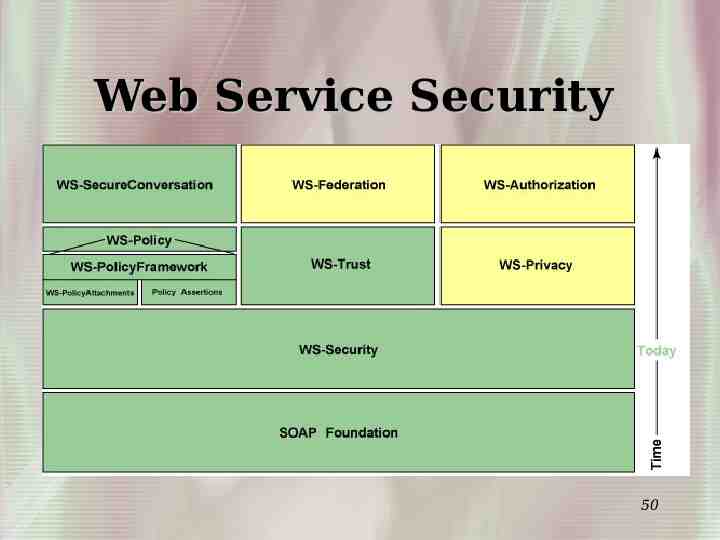
Proposed Security Specification Initial Specifications WS-Security WS-Policy WS-Trust WS-Privacy Follow-on Specifications WSSecureConversation WS-Federation 47
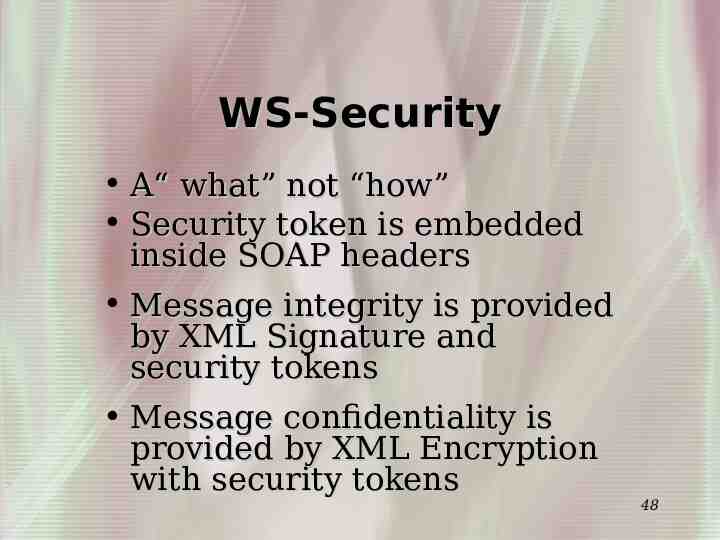
WS-Security A“ what” not “how” Security token is embedded inside SOAP headers Message integrity is provided by XML Signature and security tokens Message confidentiality is provided by XML Encryption with security tokens 48
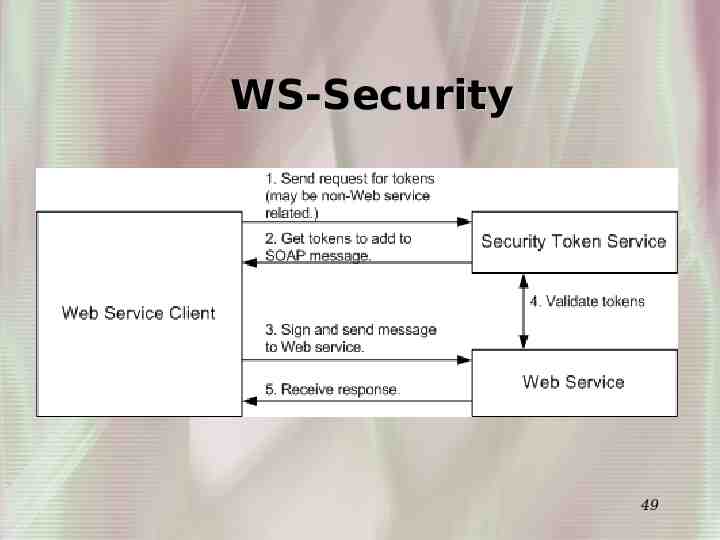
WS-Security 49
Web Service Security 50
Reference [1] [1 http://www.faqs.org/faqs/computer-security/ssltalk faq/ [2] http://www.pcwebopedia.com/TERM/S/SSL.htm [3]http://developer.netscape.com/docs/manuals/ security/sslin/contents.htm [4] http://www.ece.wpi.edu/ sunar/ee578/SSL.ppt [5] http://nas.cl.uh.edu/yang/teaching/csci5931web Security/ 51 ThesisProWS Rajiv.doc