Presented By: Manpreet Singh Randhawa CSc 253
19 Slides3.66 MB
Presented By: Manpreet Singh Randhawa CSc 253
Chat Forensics Traditional Chat Forensics Web-based Chat Forensics IM Comparison Skype Security Skype Communication Framework Skype As A Threat To Enterprise Network Security Skype Forensics – Tools Paraben Chat Examiner Belkasoft Forensic IM Analyzer Legal Issues
More and more people are communicating through chat. Popularity and purported privacy of instant messaging exploited by criminals, especially online predators. Loads of digital evidence. Digital forensic examiners need to perform a thorough analysis of chat logs, registry keys and other artifacts. Several chat programs - ICQ, Yahoo, MSN, Trillian, AIM, Hello, Skype, Miranda, Google Talk, and more. Chat rooms where people from across the world can communicate using various methods: Text Messaging, Pictures, Audio, Video, Webcam, File Sharing, etc. 3
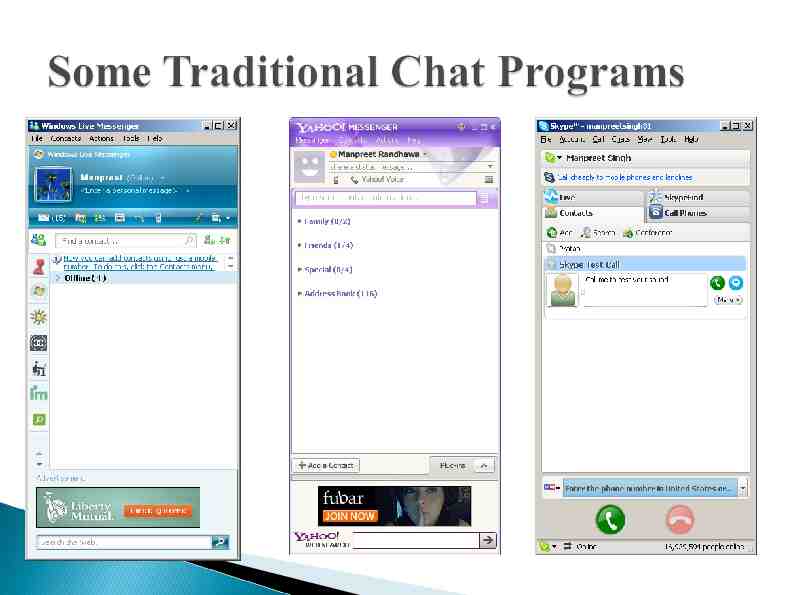
Instant messaging is the process of exchange of text messages, etc in real-time between two or more people logged into a particular instant messaging service. Client-based messaging programs such as AIM, MSN Messenger, Yahoo Messenger, etc. Require some form of installation on client machine. Users need to authenticate. Messaging server can archive the IP address of the user – pinpoint a user to a specific computer or geographical location. Conversations are not logged by messaging servers. Information can be recovered from suspect’s machine. 4
Chat logs saved on user machine as per user specification or at default location such as Program Files. Several evidentiary artifacts: Chat logs Registry keys File transfers Configuration files Archived/Deleted messages Stored “buddy” lists 5
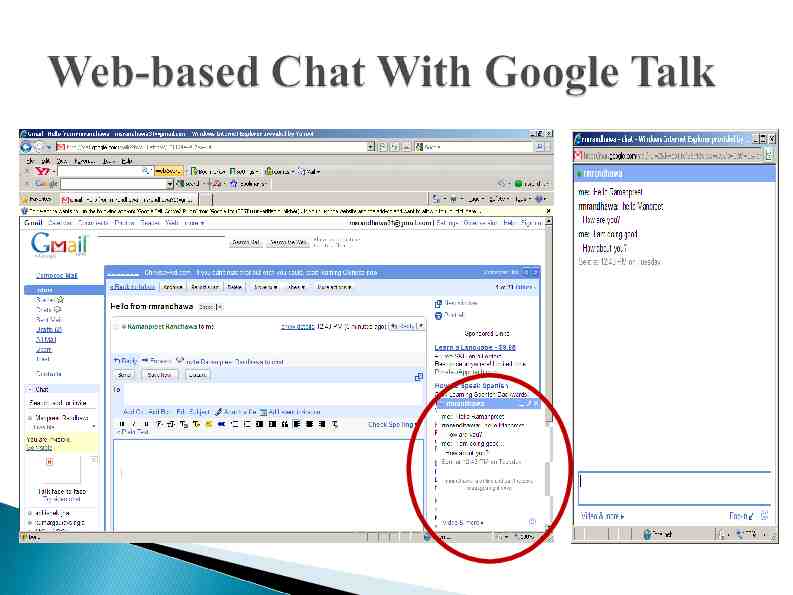
Traditional messaging clients that can be accessed using only a web browser viz. AIM Express, Google Talk, Meebo, E-Buddy, etc. Real-time messaging between two or more people using a web interface (without access to a traditional client). Volatile nature of the data and artifacts created. After web browser is closed or machine is shut down, no records of user activity or chat log archives are retained. Programs do not write to registry keys or leave configuration files on client machine. Investigators can only look at remnants of whole or partial conversations dumped to page files or unallocated space on hard disk. 7
Artifacts partially recovered include time estimate, conversation details, screen names, and buddy list details. Browser forensics come in handy. Valuable information found in: Internet cache files History.IE5 Index.dat file Temporary Internet Files\Content.IE5 Cookies Pagefile.sys 8
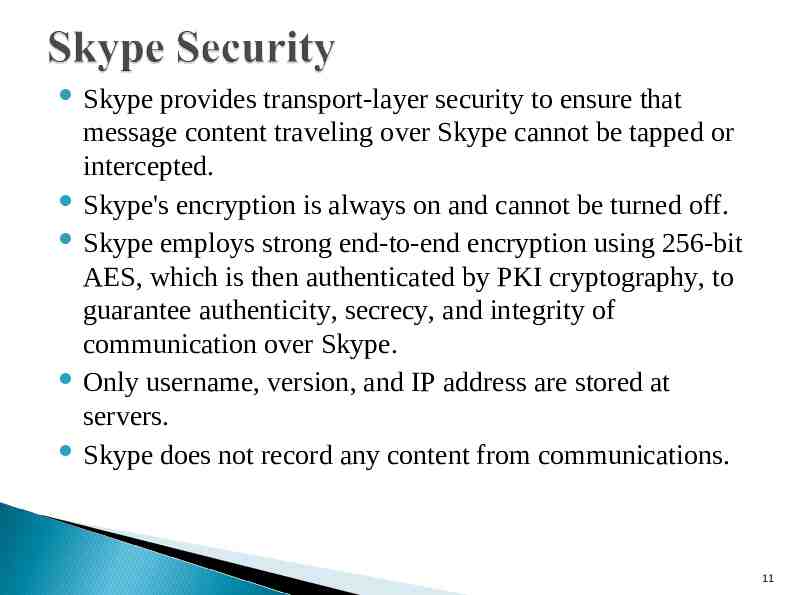
Skype provides transport-layer security to ensure that message content traveling over Skype cannot be tapped or intercepted. Skype's encryption is always on and cannot be turned off. Skype employs strong end-to-end encryption using 256-bit AES, which is then authenticated by PKI cryptography, to guarantee authenticity, secrecy, and integrity of communication over Skype. Only username, version, and IP address are stored at servers. Skype does not record any content from communications. 11
Skype HTTP Server – HS; Skype Client – SC; Super Node – SN; Registration Super Node – RSN; Authentication Super Node – ASN; Location Super Node – LSN; Neighbour Super Node – NSN;
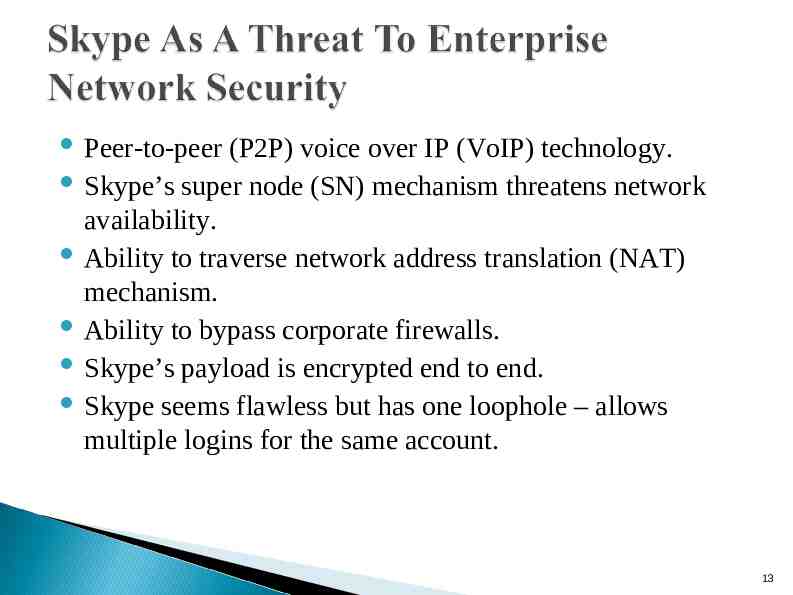
Peer-to-peer (P2P) voice over IP (VoIP) technology. Skype’s super node (SN) mechanism threatens network availability. Ability to traverse network address translation (NAT) mechanism. Ability to bypass corporate firewalls. Skype’s payload is encrypted end to end. Skype seems flawless but has one loophole – allows multiple logins for the same account. 13
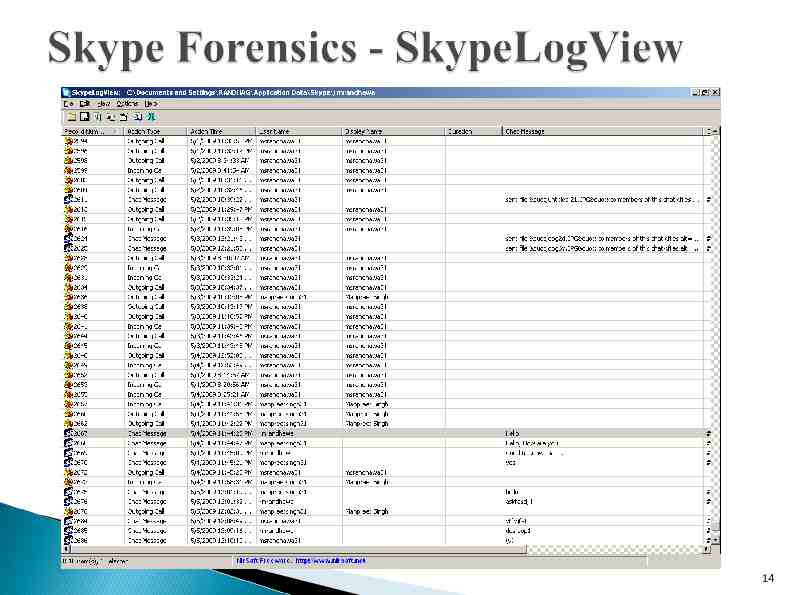
14
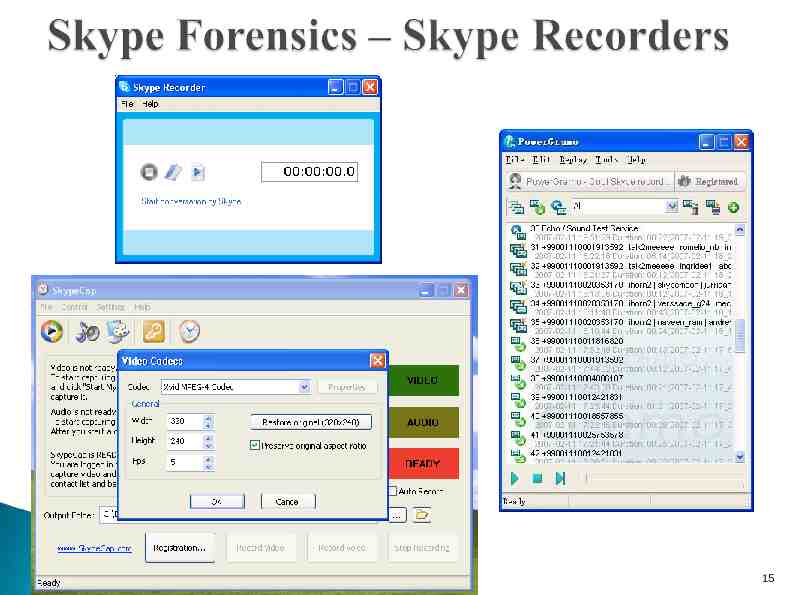
15
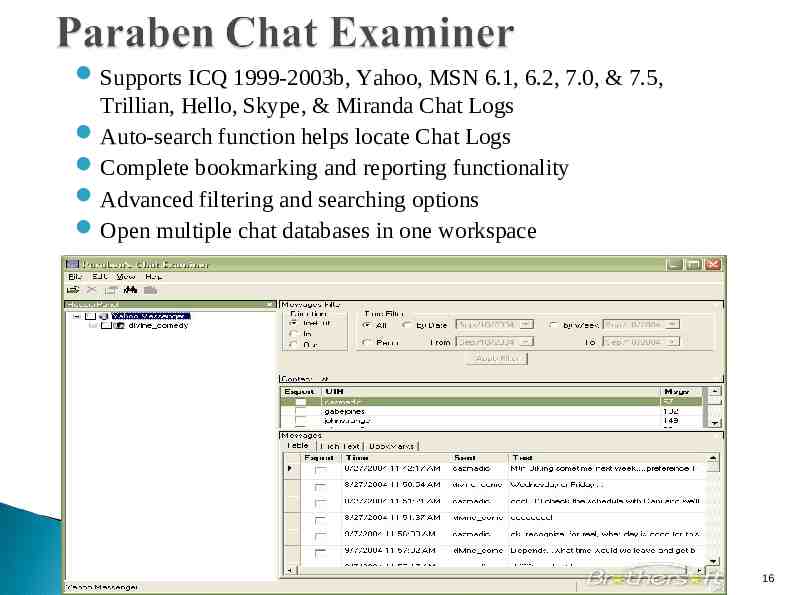
Supports ICQ 1999-2003b, Yahoo, MSN 6.1, 6.2, 7.0, & 7.5, Trillian, Hello, Skype, & Miranda Chat Logs Auto-search function helps locate Chat Logs Complete bookmarking and reporting functionality Advanced filtering and searching options Open multiple chat databases in one workspace 16
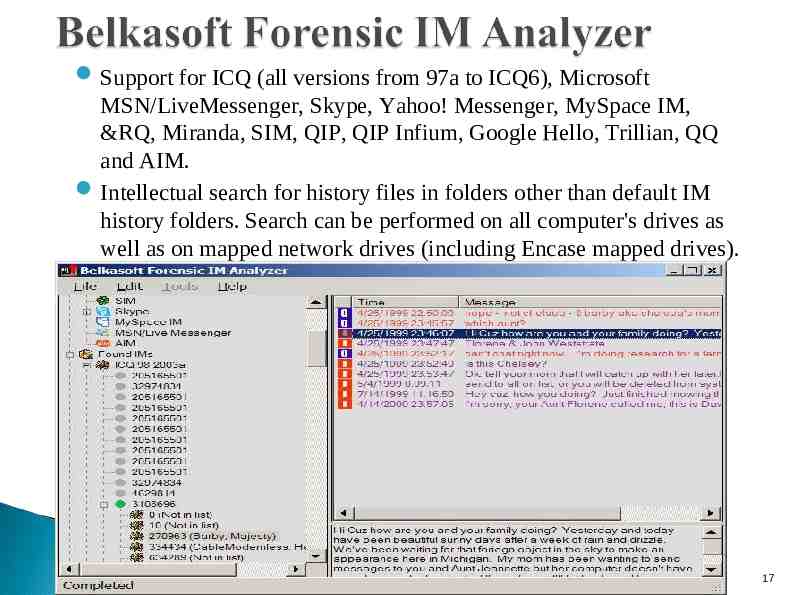
Support for ICQ (all versions from 97a to ICQ6), Microsoft MSN/LiveMessenger, Skype, Yahoo! Messenger, MySpace IM, &RQ, Miranda, SIM, QIP, QIP Infium, Google Hello, Trillian, QQ and AIM. Intellectual search for history files in folders other than default IM history folders. Search can be performed on all computer's drives as well as on mapped network drives (including Encase mapped drives). 17
United States v. Jackson, 2007 WL 1381772 (D. Neb. May 8, 2007). In a criminal case, the defendant filed a motion in limine to exclude evidence of chat room conversations. At the conclusion of each chat room session, an undercover police officer conducting the chat room conversation would cut-andpaste the entire conversation into a word document for later review. However, a computer forensics expert testified that this cut-and-paste method created several errors and that several portions of the defendant’s conversations were omitted. The defendant argued the omitted portions of the transcript contained evidence relating directly to his intent and should not be admitted as evidence. The court found that the cut-and-paste document was not admissible evidence at trial because it was not authentic under the Federal Rules of Evidence. 18
Thank You! 19