Overview of Distributed Denial of Service (DDoS) Wei Zhou
19 Slides372.50 KB
Overview of Distributed Denial of Service (DDoS) Wei Zhou
Outline of the presentation DDoS definition and its attacking architectures DDoS classification Defense mechanism classification – Reactive VS. Proactive – Classification by defending front-line SOS – a case study
What is it? – No ready-to-go definition available – Characteristics – Multiple attackers vs. single victim To cause denial of service to legitimate users on the victim Two major attacking architecture Direct attack Reflector attack
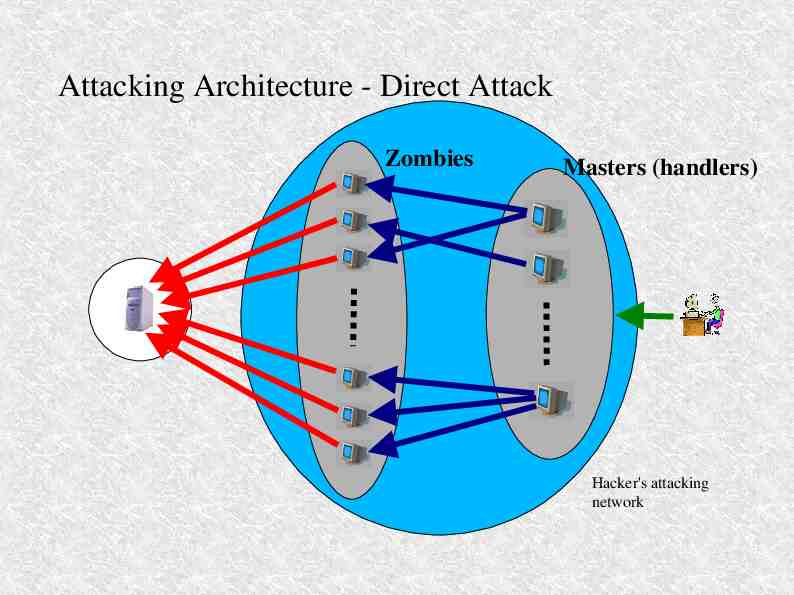
Attacking Architecture - Direct Attack Zombies Masters (handlers) Hacker's attacking network
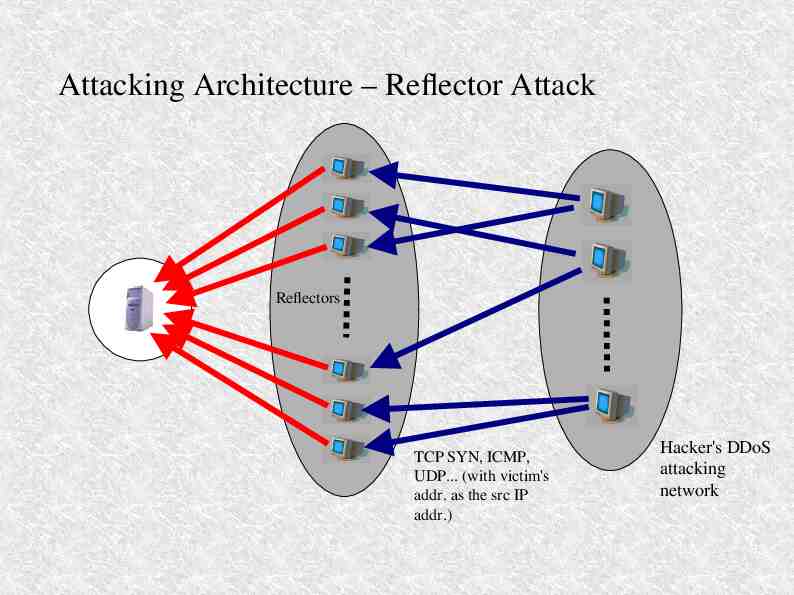
Attacking Architecture – Reflector Attack Reflectors TCP SYN, ICMP, UDP. (with victim's addr. as the src IP addr.) Hacker's DDoS attacking network
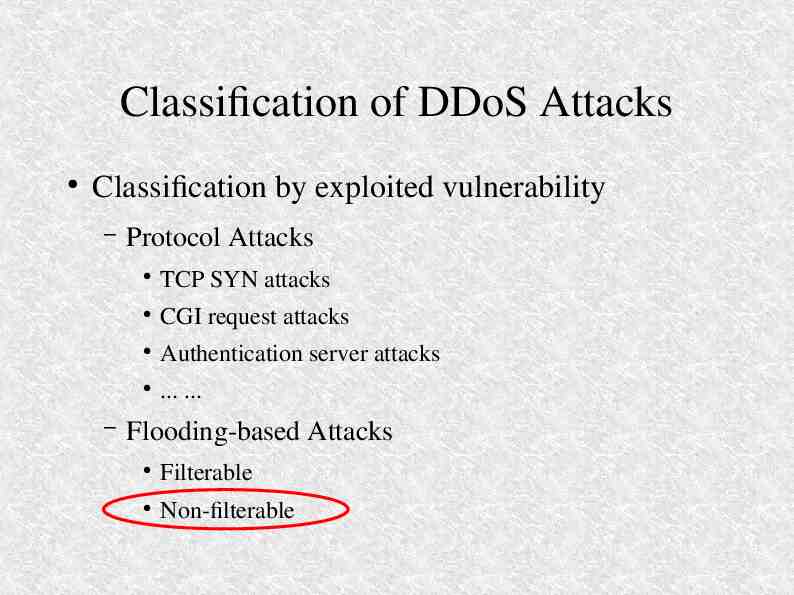
Classification of DDoS Attacks Classification by exploited vulnerability – – Protocol Attacks TCP SYN attacks CGI request attacks Authentication server attacks . . Flooding-based Attacks Filterable Non-filterable
Defense Mechanisms Classification by activity level – – Reactive mechanisms Easy to be deployed Hard to tell good guys from bad guys Inflexible to adapt new attacks Proactive mechanisms Motivations to deploy Accuracy on differentiating packets
Defense Mechanisms (cont.) Classification by defending front-line – Victim network – Intermediate network – Source network
At the victim side IDS plus Firewall – Detect bogus packets based on well-known attack signatures – Flexibility Puzzle solving by clients – Client must solve a puzzle (small scripts, cookies etc.) in order to access server's resources – Efficiency Duplicate server resources – Distribute server resources into more places – Synchronization, costs etc. Victim network can't do NOTHING if its link(s) to the ISP is jammed
In the intermediate network IP traceback – Can be used to collect forensic evidence – (Need further exploration on this topic) Push-back mechanism Route-Based packet filtering Overlay network
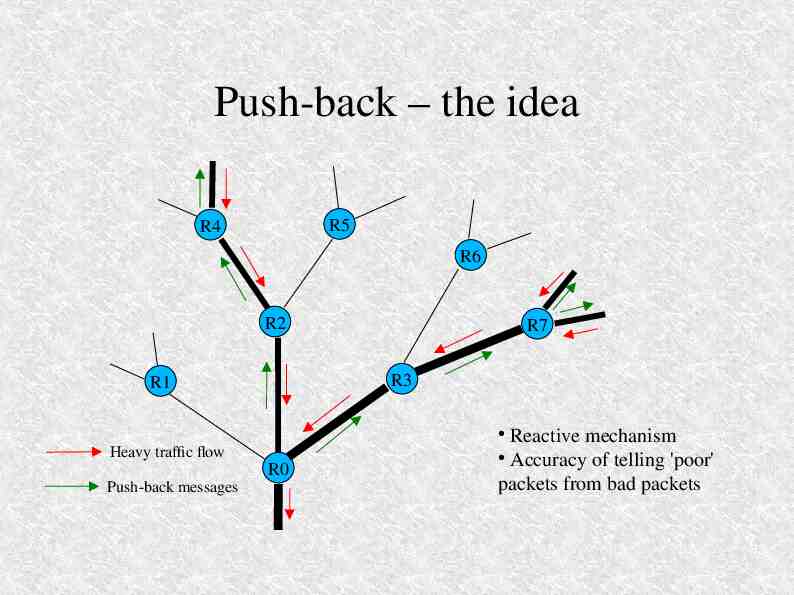
Push-back – the idea R5 R4 R6 R2 R7 R3 R1 Reactive mechanism Accuracy of telling 'poor' packets from bad packets Heavy traffic flow R0 Push-back messages
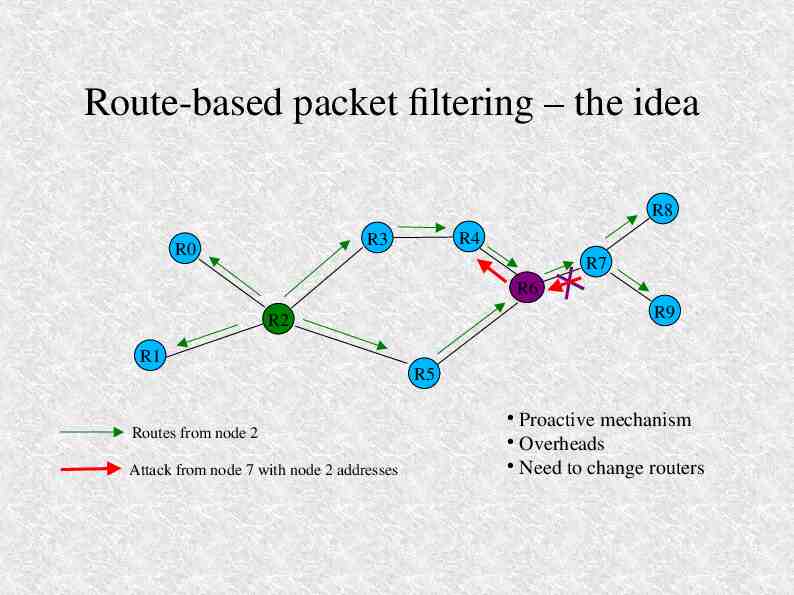
Route-based packet filtering – the idea R8 R4 R3 R0 R7 R6 R9 R2 R1 R5 Proactive mechanism Overheads Need to change routers Routes from node 2 Attack from node 7 with node 2 addresses
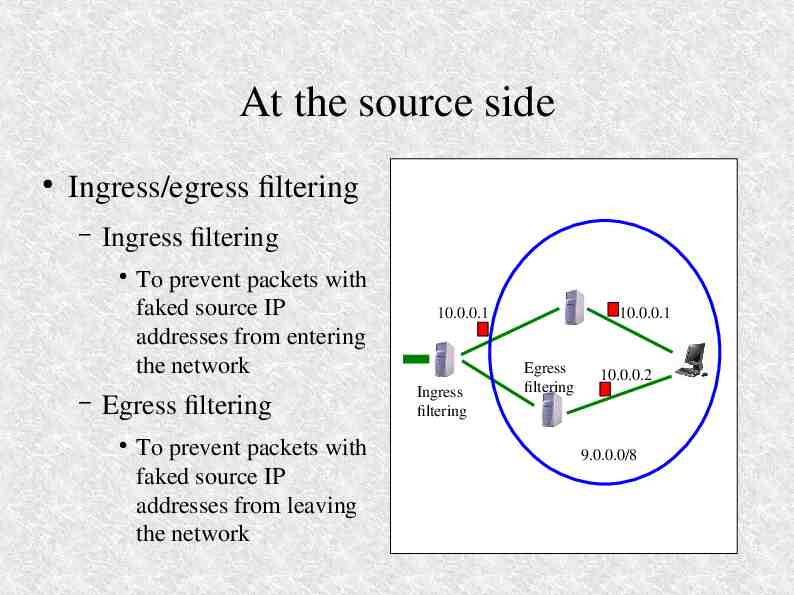
At the source side Ingress/egress filtering – Ingress filtering – To prevent packets with faked source IP addresses from entering the network Egress filtering To prevent packets with faked source IP addresses from leaving the network 10.0.0.1 10.0.0.1 Ingress filtering Egress filtering 10.0.0.2 9.0.0.0/8
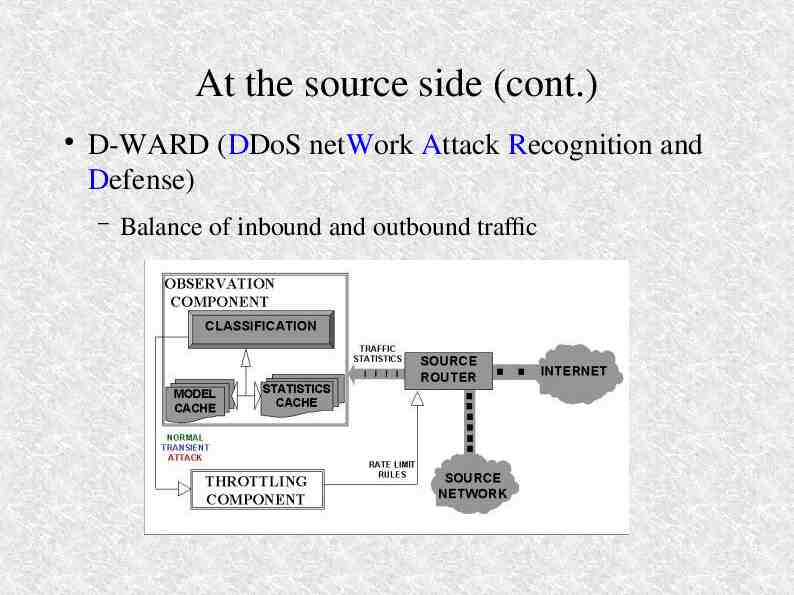
At the source side (cont.) D-WARD (DDoS netWork Attack Recognition and Defense) – Balance of inbound and outbound traffic
D-WARD (cont.) Motivation of deployment Asymmetric problems Source network
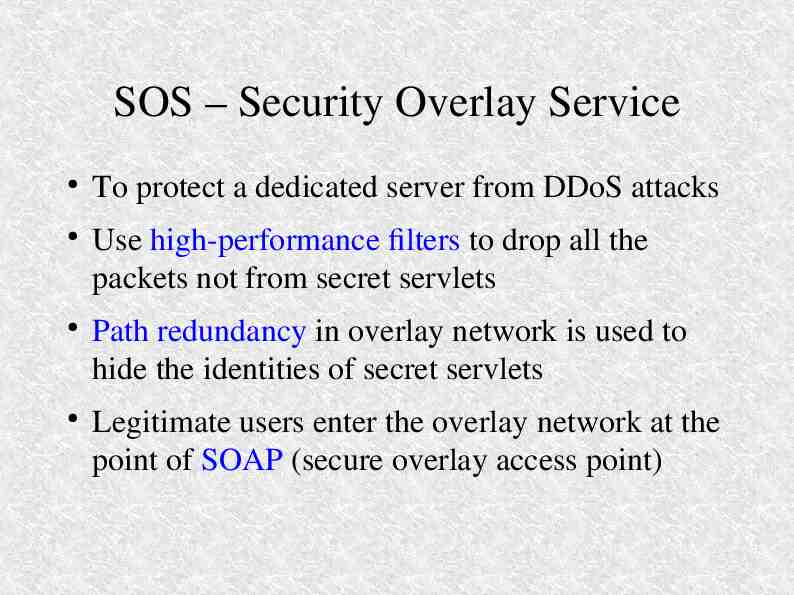
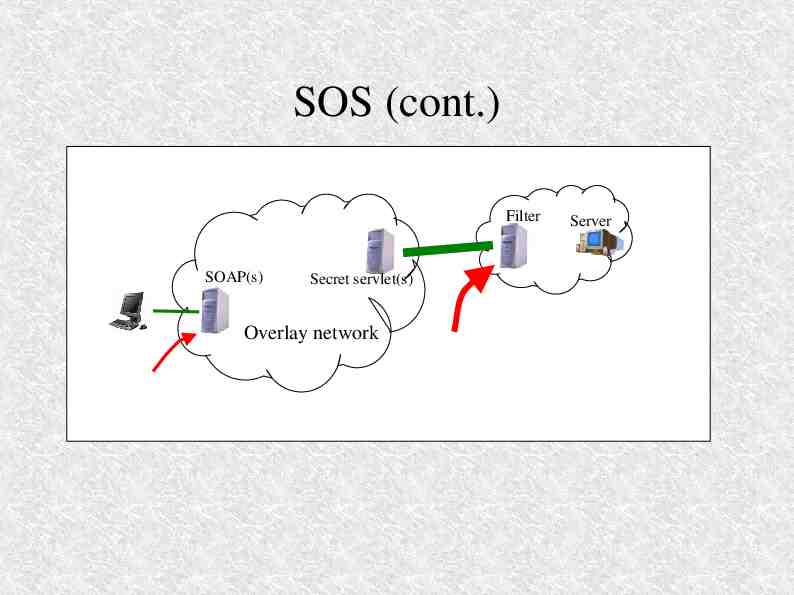
SOS – Security Overlay Service To protect a dedicated server from DDoS attacks Use high-performance filters to drop all the packets not from secret servlets Path redundancy in overlay network is used to hide the identities of secret servlets Legitimate users enter the overlay network at the point of SOAP (secure overlay access point)
SOS (cont.) Filter SOAP(s) Server Secret servlet(s) Overlay network Big time delay
References R. K. C. Chang, “Defending against Flooding-Based Distributed Denial-ofSevice Attacks: A Tutorial” P. Ferguson and D. Senie, “Network Ingress Filtering: Defeating Denial of Service Attacks which employ IP Source Address Spoofing”, RFC 2827 J. Ioannidis and S. M. Bellovin, “Implementing Pushback: Router-Based Defense Against DDoS Attacks” A. D. Keromytis, V. Misra and D. Rubenstein, “SOS: Secure Overlay Services” R. Mahajan, S. M. Bellovin, S. Floyd, J. Ioannidis, V. Paxson and S. Shenker, “Controlling High Bandwidth Aggregates in the Network” J. Mirkovic, J. Martin and P. Reiher, “A Taxonomy of DDoS Attacks and DDoS Defense Mechanisms” J. Mirkovic, G. Prier and P. Reiher, “Attacking DDoS at the Source” K. Park and H. Lee, “A Proactive Approach to Distributed DoS Attack Prevention using Route-Based Packet Filtering”
Thank you!