Location Based Services and Privacy Issues Tsovinar
16 Slides554.30 KB
Location Based Services and Privacy Issues Tsovinar Chugaszyan Presentation date 07.02.11
Outline LBS Technologies -Main components -Infrastructure -Applications Privacy in LBS -Threats and concerns -Solutions for privacy-preserving LBS -Analysis and challenges 2
Location Based Services Main idea: utilize the location information of the user in order to provide different services One of the most important Value-Added Services in the mobile market The first commercial LBS service: introduced in 2001 by Japanese mobile operator NTT-DoCoMo, 3
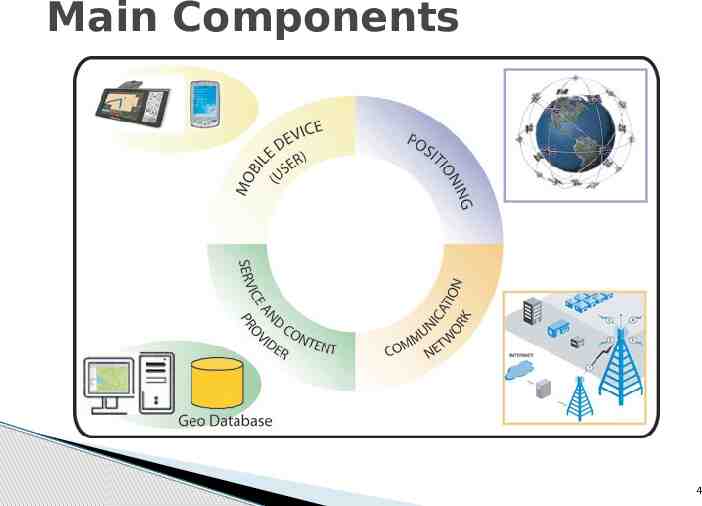
Main Components 4
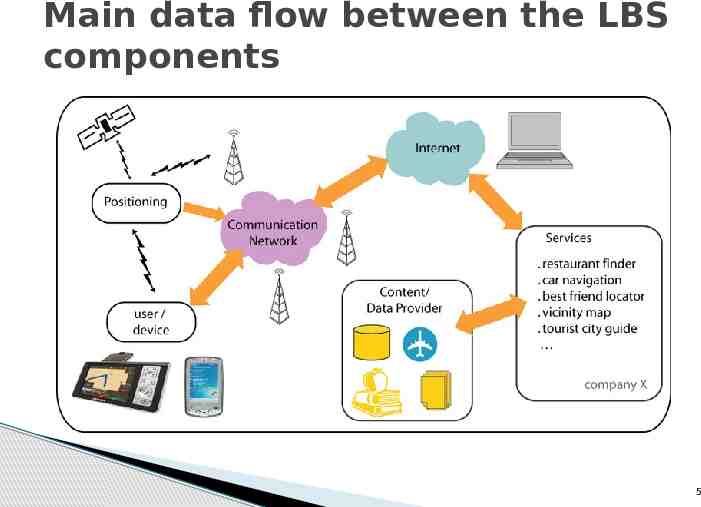
Main data flow between the LBS components 5
LBS Applications Categories and examples of applications Information services – requesting the rearest ATM Navigation - how to reach the specified target location Emergency - person who is in a need of ambulance and is lost in woods Entertainment – social networking, mobile games Marketing – location-based mobile advertising Tracking – tracking of postal packages 6
Privacy and Security Issues Revealing of sensitive information about an individual or a union. There are already some real life incidents Social networking platforms: Google Latitude, FourSquere, Gowalla, Facebook raise safety issues of the user's movement tracking records Misuse of location information may also have commercial purposes 7
Existing solutions for privacy protection: Legal Frameworks Aim to protect and preserve the privacy of the user's personal data (e.g. Directive on privacy and electronic communications by The European Parliament and the Council of the European Union) Main point: the user must be able to control the availability of her location information, i.e. who can access it and for what purposes Used in conjunction with technical Solutions 8
Existing solutions for privacy protection: Technical Solutions The 3 main categories of Privacy-Enhancing Technologies: Cryptographic Encryption techniquessecurity mechanisms providing location authentication and authorization. Pseudonymization techniques- replace the user's actual identity with an artificial one (pseudonym). Location anonymization techniquestransform the precise location of the user into a cloaked spatial area. 9
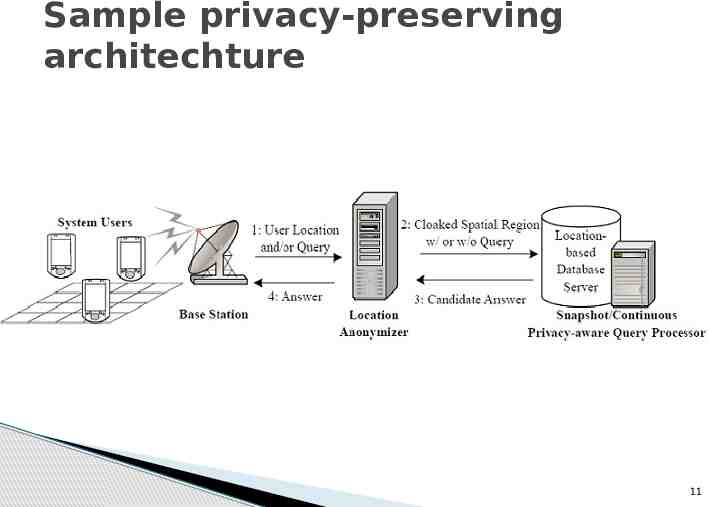
Location Anonymization Main idea: the exact location information of the user gets transformed into cloaked location areas Metric: k-anonymity, indicates that the user prefers to be not distinguishable among k users The most famous model: Trusted Third Party paradigm, which utilizes a middle layer between the mobile device and the database server 10
Sample privacy-preserving architechture 11
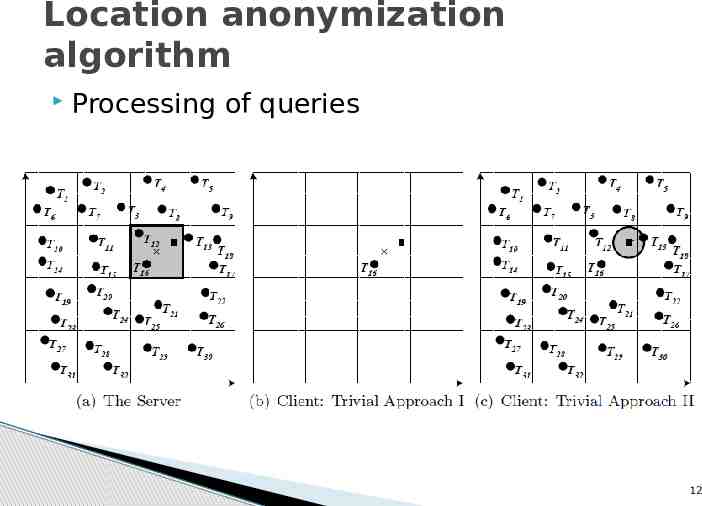
Location anonymization algorithm Processing of queries 12
Analysis TTP Advantages : suitable for real time applications requires less operating costs. TTP Drawbacks : trust vs. financial obligations creates risks of compromising the privacy in case trusted party gets attacked 13
The Main Challenge The tradeoff between privacy and the quality of service that the LBS can provide. The strong solution is the one which provides best balance “ .develop customizable privacy protection mechanisms that can help users find a comfortable balance between the extreme of fully disclosed location data and the extreme of completely withheld location data.„(L. Liu) 14
Special thanks to our tutors and to all reviewers of my work for very helpful remarks 15
Thank you for your attention! 16