Introduction to TCP/IP networking Source: Ganesh Sittampalam
29 Slides116.00 KB
Introduction to TCP/IP networking Source: Ganesh Sittampalam
TCP/IP protocol family IP : Internet Protocol – UDP : User Datagram Protocol RTP, traceroute – TCP : Transmission Control Protocol HTTP, FTP, ssh
What is an internet? A set of interconnected networks The Internet is the most famous example Networks can be completely different – Ethernet, ATM, modem, – (TCP/)IP is what links them
What is an internet? (cont) Routers are devices on multiple networks that pass traffic between them Individual networks pass traffic from one router or endpoint to another TCP/IP hides the details as much as possible
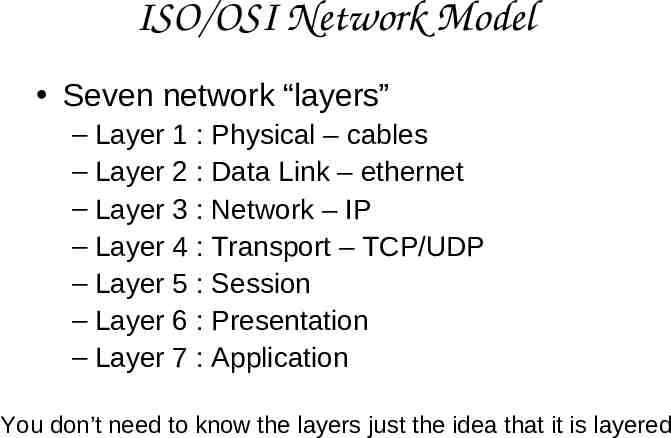
ISO/OSI Network Model Seven network “layers” – Layer 1 : Physical – cables – Layer 2 : Data Link – ethernet – Layer 3 : Network – IP – Layer 4 : Transport – TCP/UDP – Layer 5 : Session – Layer 6 : Presentation – Layer 7 : Application You don’t need to know the layers just the idea that it is layered
TCP/IP Network Model Different view – 4 layers – Layer 1 : Link – Layer 2 : Network – Layer 3 : Transport – Layer 4 : Application
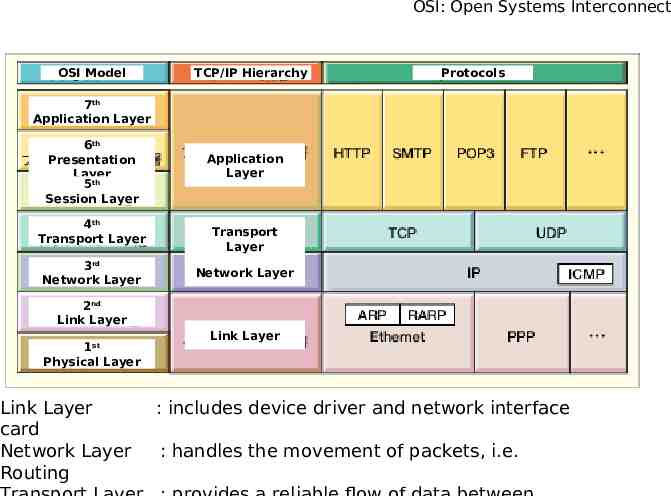
OSI: Open Systems Interconnect OSI and Protocol Stack OSI Model TCP/IP Hierarchy Protocols 7 Application Layer th 6th Presentation Layer 5th Session Layer 4th Transport Layer 3rd Network Layer Application Layer Transport Layer Network Layer 2nd Link Layer 1st Physical Layer Link Layer card Network Layer Routing Link Layer : includes device driver and network interface : handles the movement of packets, i.e.
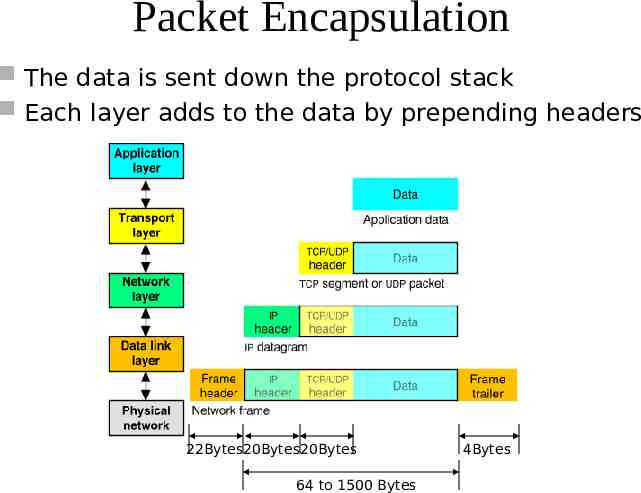
Packet Encapsulation The data is sent down the protocol stack Each layer adds to the data by prepending headers 22Bytes20Bytes20Bytes 64 to 1500 Bytes 4Bytes
IP Responsible for end to end transmission Sends data in individual packets Maximum size of packet is determined by the networks – Fragmented if too large Unreliable – Packets might be lost, corrupted, duplicated, delivered out of order
IP addresses 4 bytes – e.g. 163.1.125.98 – Each device normally gets one (or more) – In theory there are about 4 billion available But
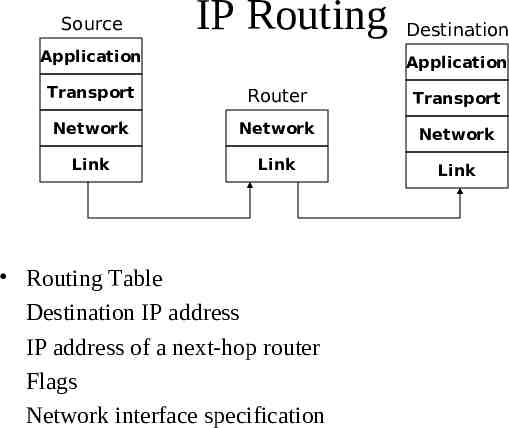
Routing How does a device know where to send a packet? – All devices need to know what IP addresses are on directly attached networks – If the destination is on a local network, send it directly there
Routing (cont) If the destination address isn’t local – Most non-router devices just send everything to a single local router – Routers need to know which network corresponds to each possible IP address
Allocation of addresses Controlled centrally by ICANN – Fairly strict rules on further delegation to avoid wastage Have to demonstrate actual need for them Organizations that got in early have bigger allocations than they really need
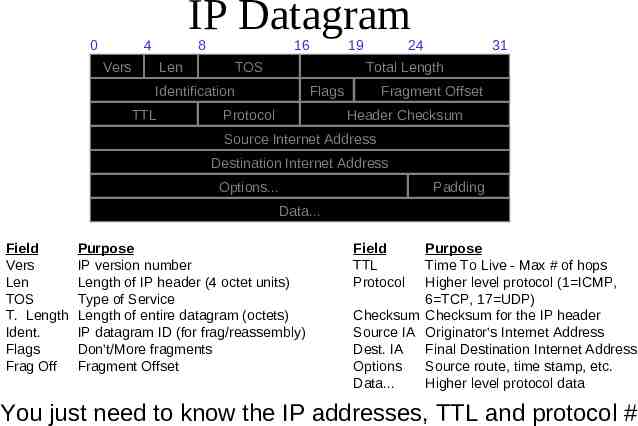
IP packets Source and destination addresses Protocol number – 1 ICMP, 6 TCP, 17 UDP Various options – e.g. to control fragmentation Time to live (TTL) – Prevent routing loops
0 IP Datagram 4 8 Vers 16 Len TOS 24 31 Total Length Identification TTL 19 Flags Protocol Fragment Offset Header Checksum Source Internet Address Destination Internet Address Options. Padding Data. Field Vers Len TOS T. Length Ident. Flags Frag Off Purpose IP version number Length of IP header (4 octet units) Type of Service Length of entire datagram (octets) IP datagram ID (for frag/reassembly) Don’t/More fragments Fragment Offset Field TTL Protocol Purpose Time To Live - Max # of hops Higher level protocol (1 ICMP, 6 TCP, 17 UDP) Checksum Checksum for the IP header Source IA Originator’s Internet Address Dest. IA Final Destination Internet Address Options Source route, time stamp, etc. Data. Higher level protocol data You just need to know the IP addresses, TTL and protocol #
Source IP Routing Application Destination Application Transport Router Transport Network Network Network Link Link Link Routing Table Destination IP address IP address of a next-hop router Flags Network interface specification
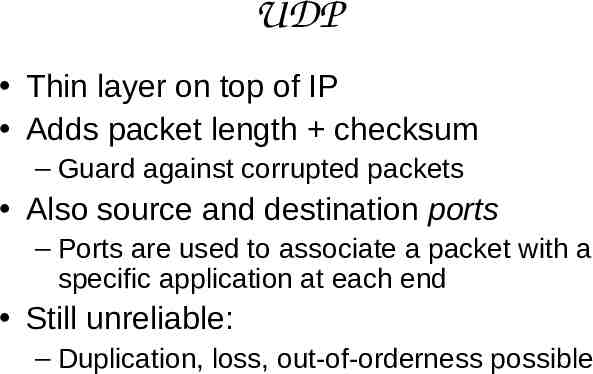
UDP Thin layer on top of IP Adds packet length checksum – Guard against corrupted packets Also source and destination ports – Ports are used to associate a packet with a specific application at each end Still unreliable: – Duplication, loss, out-of-orderness possible
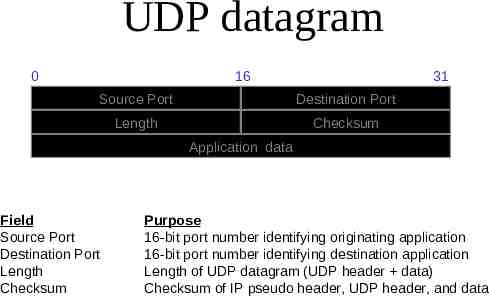
UDP datagram 0 16 31 Source Port Destination Port Length Checksum Application data Field Source Port Destination Port Length Checksum Purpose 16-bit port number identifying originating application 16-bit port number identifying destination application Length of UDP datagram (UDP header data) Checksum of IP pseudo header, UDP header, and data
Typical applications of UDP – Where packet loss etc is better handled by the application than the network stack – Where the overhead of setting up a connection isn’t wanted VOIP NFS – Network File System Most games
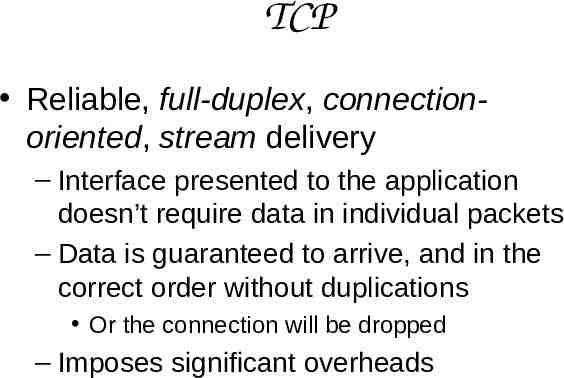
TCP Reliable, full-duplex, connectionoriented, stream delivery – Interface presented to the application doesn’t require data in individual packets – Data is guaranteed to arrive, and in the correct order without duplications Or the connection will be dropped – Imposes significant overheads
Applications of TCP Most things! – HTTP, FTP, Saves the application a lot of work, so used unless there’s a good reason not to
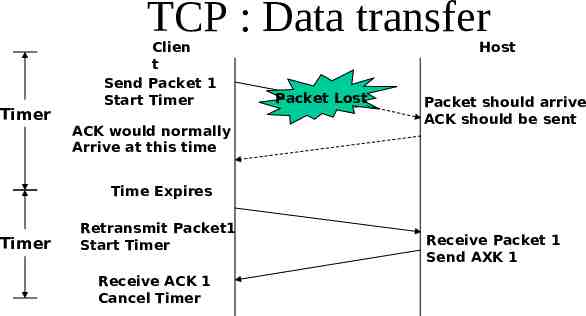
TCP implementation Connections are established using a three-way handshake Data is divided up into packets by the operating system Packets are numbered, and received packets are acknowledged Connections are explicitly closed – (or may abnormally terminate)
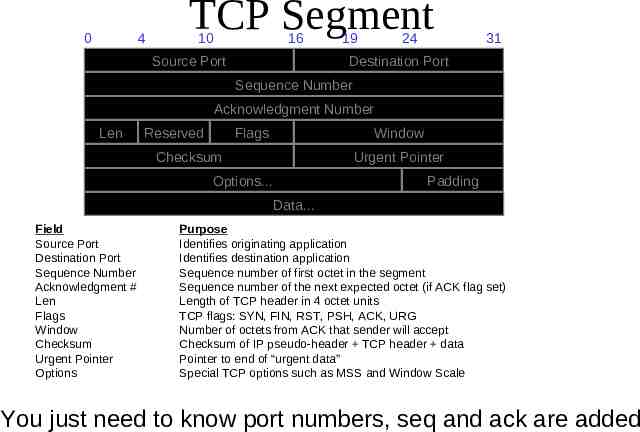
TCP Packets Source destination ports Sequence number Acknowledgement number Checksum Various options
0 4 TCP Segment 10 16 Source Port 19 24 31 Destination Port Sequence Number Acknowledgment Number Len Reserved Flags Window Checksum Urgent Pointer Options. Padding Data. Field Source Port Destination Port Sequence Number Acknowledgment # Len Flags Window Checksum Urgent Pointer Options Purpose Identifies originating application Identifies destination application Sequence number of first octet in the segment Sequence number of the next expected octet (if ACK flag set) Length of TCP header in 4 octet units TCP flags: SYN, FIN, RST, PSH, ACK, URG Number of octets from ACK that sender will accept Checksum of IP pseudo-header TCP header data Pointer to end of “urgent data” Special TCP options such as MSS and Window Scale You just need to know port numbers, seq and ack are added
TCP : Data transfer Timer Clien t Send Packet 1 Start Timer ACK would normally Arrive at this time Host Packet Lost Packet should arrive ACK should be sent Time Expires Timer Retransmit Packet1 Start Timer Receive ACK 1 Cancel Timer Receive Packet 1 Send AXK 1
IPv6 128 bit addresses – Make it feasible to be very wasteful with address allocations Lots of other new features – Built-in autoconfiguration, security options, Not really in production use yet
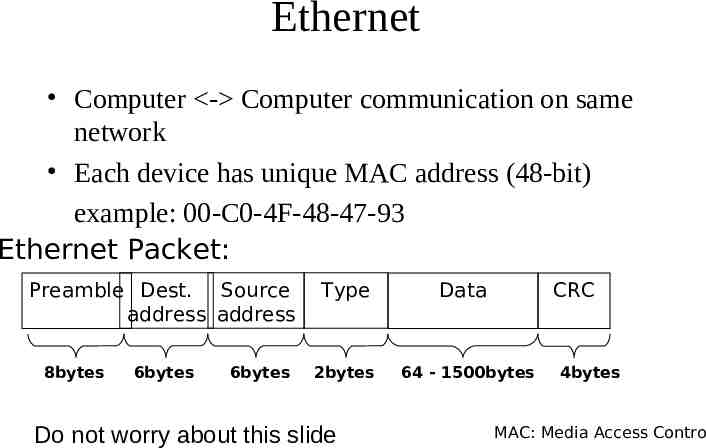
Ethernet Computer - Computer communication on same network Each device has unique MAC address (48-bit) example: 00-C0-4F-48-47-93 Ethernet Packet: Preamble Dest. Source address address 8bytes 6bytes 6bytes Type 2bytes Do not worry about this slide Data CRC 64 - 1500bytes 4bytes MAC: Media Access Contro
ARP : Address Resolution Protocol ARP provides mapping 32bit IP address - 48bit MAC address 128.97.89.153 - 00-C0-4F-48-47-93 ARP cache maintains the recent mappings from IP addresses to MAC addresses Protocol 1. ARP request broadcast on Ethernet 2. Destination host ARP layer responds Do not worry about this slide
DHCP Dynamic Host Configuration Protocol – Used to tell a computer what IP address to use – Device broadcasts a request from IP 0.0.0.0 If it had an IP address before, asks for the same one again – Server (or relay) on local network responds telling it which to use (or ignores it, or tells it go away) “Lease time” telling it how long that IP will be valid for Device requests renewal of lease after ¾(?) elapsed Do not worry about this slide