Dobrodošli!
43 Slides4.92 MB
Dobrodošli!
Dobrodošli Peter Novak [email protected] EPG Manager, Microsoft Slovenija Copyright 2006 Microsoft Corp & Project Botticelli Ltd. E&OE. For informational purposes only. No warranties of any kind are made and you have to verify all information before relying on it. You can re-use this presentation as long as you read, agree, and follow the guidelines described in the “Comments” field in File/Properties.
Identity and Access Management in Heterogeneous Environments Rafał Łukawiecki Strategic Consultant, Project Botticelli Ltd [email protected] www.projectbotticelli.co.uk Copyright 2006 Microsoft Corp & Project Botticelli Ltd. E&OE. For informational purposes only. No warranties of any kind are made and you have to verify all information before relying on it. You can re-use this presentation as long as you read, agree, and follow the guidelines described in the “Comments” field in File/Properties.
5 Special Thanks This seminar was prepared with the help of: Oxford Computer Group Ltd Expertise in Identity and Access Management (Microsoft Partner) IT Service Delivery and Training www.oxfordcomputergroup.com Microsoft, with special thanks to: Daniel Meyer – thanks for many slides Steven Adler, Ronny Bjones, Olga Londer – planning and reviewing Philippe Lemmens, Detlef Eckert – Sponsorship Bas Paumen & NGN - feedback
6 Welcome! Our Objectives: Clarify the complex field of identity and access management Start a discussion about IAM in the community, so that the solutions and products are no longer “Best Kept Secrets” Show you how to better realise value and optimise costs of dealing with identities Outline the future Our Plan: One overview session – concepts and ideas Three specialised sessions - technology
7 Logistics You will receive a paper evaluation form. Please complete it as your feedback is very important to us. You can also contact Matjaz at [email protected] All PowerPoint presentations will be available for download. Please ask questions at any time you wish. Additionally, I will be available to take questions after my last session today.
Identity and Access Management: Overview Rafal Lukawiecki Strategic Consultant, Project Botticelli Ltd [email protected] www.projectbotticelli.co.uk Copyright 2006 Microsoft Corp & Project Botticelli Ltd. E&OE. For informational purposes only. No warranties of any kind are made and you have to verify all information before relying on it. You can re-use this presentation as long as you read, agree, and follow the guidelines described in the “Comments” field in File/Properties. This presentation is based on work of many authors from Microsoft, Oxford Computer Group and other companies. Please see the “Introductions” presentation for acknowledgments.
9 Objectives Build a good conceptual background to enable later technical discussions of the subject Overview the problems and opportunities in the field of identity and access management Introduce terminology Highlight a possible future direction
10 Session Agenda Identity Problem of Today Identity Laws and Metasystem Components and Terminology Roadmap
11 Identity Problem of Today
12 Universal Identity? Internet was build so that communications are anonymous In-house networks use multiple, often mutuallyincompatible, proprietary identity systems Users are incapable of handling multiple identities Criminals love to exploit this mess
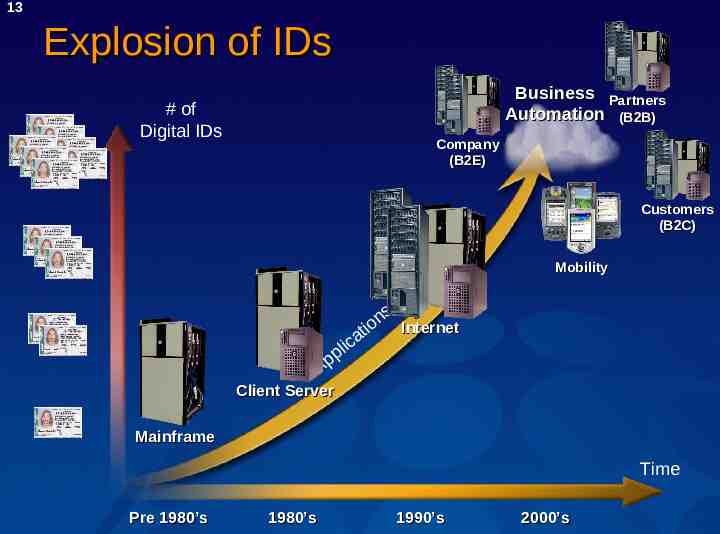
13 Explosion of IDs Business Partners Automation (B2B) # of Digital IDs Company (B2E) Customers (B2C) Mobility ns it o Internet ica l p p A Client Server Mainframe Time Pre 1980’s 1980’s 1990’s 2000’s
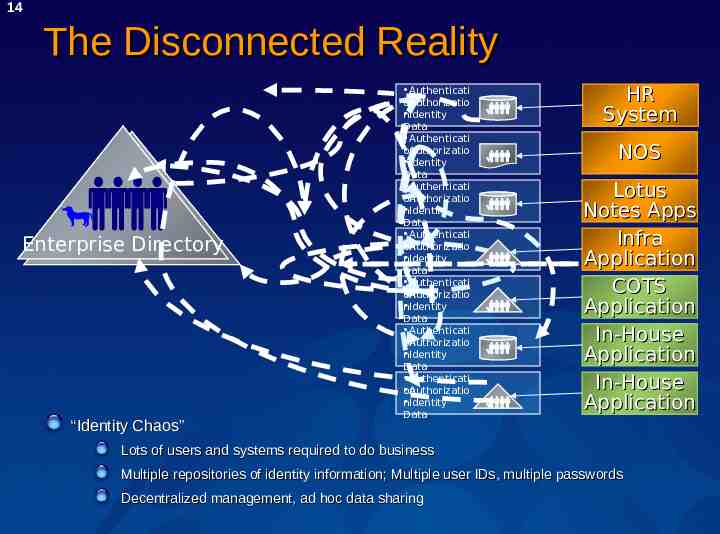
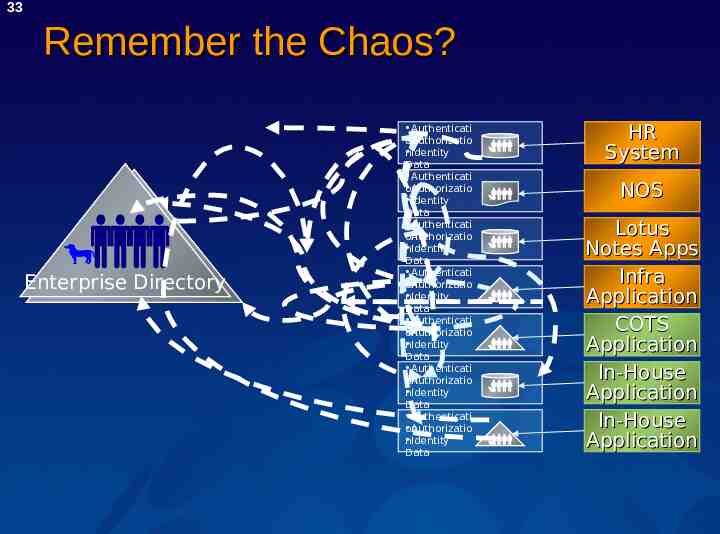
14 The Disconnected Reality Enterprise Directory “Identity Chaos” Authenticati Authorizatio on Identity n Data Authenticati Authorizatio on Identity n Data Authenticati Authorizatio on Identity n Data Authenticati Authorizatio on Identity n Data Authenticati Authorizatio on Identity n Data Authenticati Authorizatio on Identity n Data Authenticati Authorizatio on Identity n Data HR System NOS Lotus Notes Apps Infra Application COTS Application In-House Application In-House Application Lots of users and systems required to do business Multiple repositories of identity information; Multiple user IDs, multiple passwords Decentralized management, ad hoc data sharing
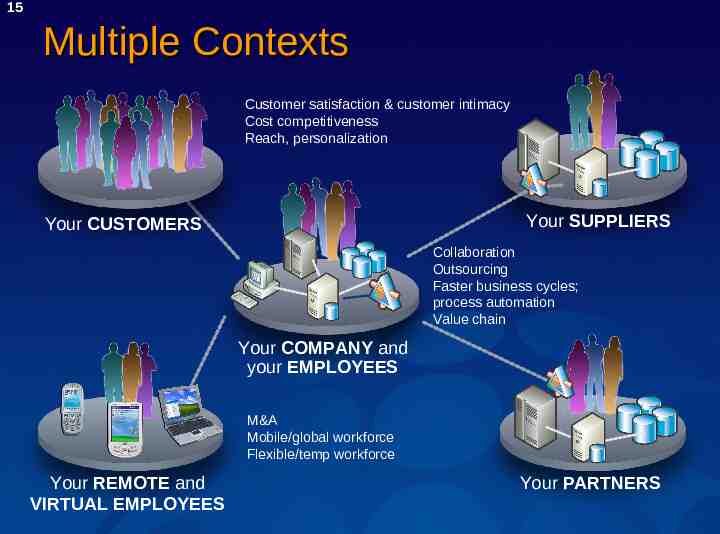
15 Multiple Contexts Customer satisfaction & customer intimacy Cost competitiveness Reach, personalization Your SUPPLIERS Your CUSTOMERS Collaboration Outsourcing Faster business cycles; process automation Value chain Your COMPANY and your EMPLOYEES M&A Mobile/global workforce Flexible/temp workforce Your REMOTE and VIRTUAL EMPLOYEES Your PARTNERS
16 Trends Impacting Identity Rising Tide of Regulation and Compliance SOX, HIPAA, GLB, Basel II, 21 CFR Part 11, 15.5 billion spend in 2005 on compliance (analyst estimate) Deeper Line of Business Automation and Integration One half of all enterprises have SOA under development Web services spending growing 45% CAGR Increasing Threat Landscape Identity theft costs banks and credit card issuers 1.2 billion in 1 yr 250 billion lost in 2004 from exposure of confidential info Maintenance Costs Dominate IT Budget On average employees need access to 16 apps and systems Companies spend 20-30 per user per year for PW resets Data Sources: Gartner, AMR Research, IDC, eMarketer, U.S. Department. of Justice
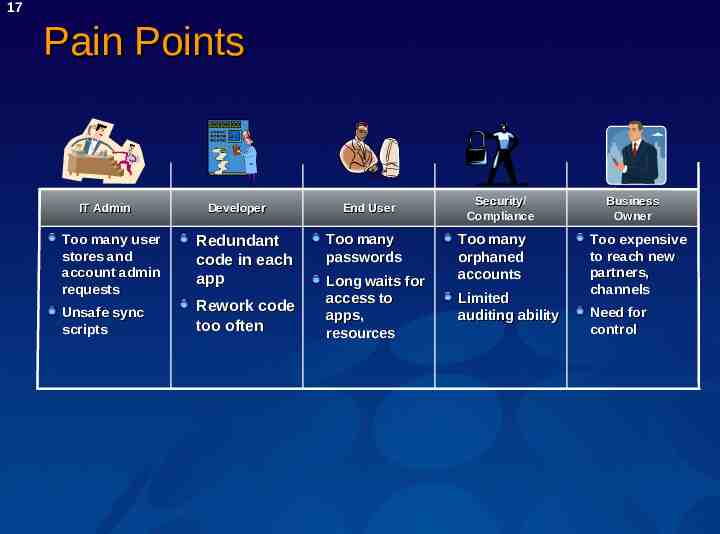
17 Pain Points IT Admin Too many user stores and account admin requests Unsafe sync scripts Developer Redundant code in each app Rework code too often End User Too many passwords Long waits for access to apps, resources Security/ Compliance Too many orphaned accounts Limited auditing ability Business Owner Too expensive to reach new partners, channels Need for control
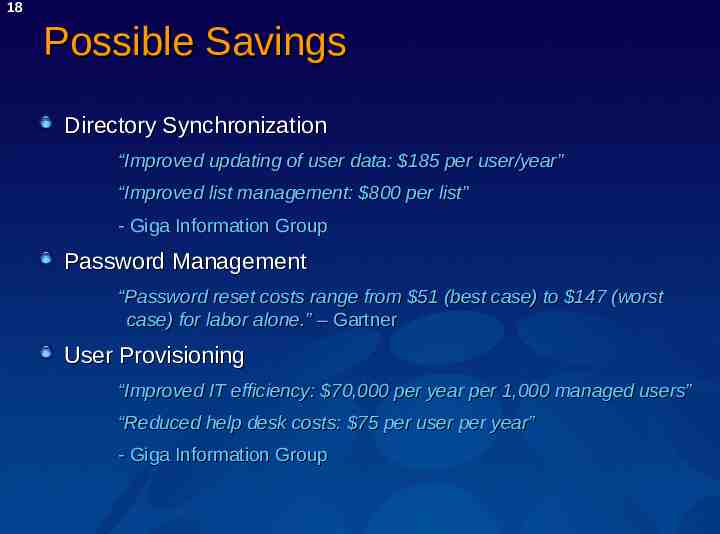
18 Possible Savings Directory Synchronization “Improved updating of user data: 185 per user/year” “Improved list management: 800 per list” - Giga Information Group Password Management “Password reset costs range from 51 (best case) to 147 (worst case) for labor alone.” – Gartner User Provisioning “Improved IT efficiency: 70,000 per year per 1,000 managed users” “Reduced help desk costs: 75 per user per year” - Giga Information Group
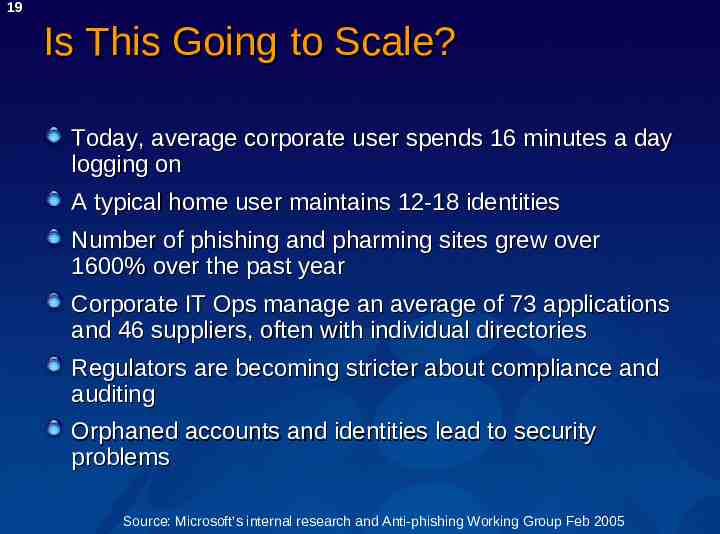
19 Is This Going to Scale? Today, average corporate user spends 16 minutes a day logging on A typical home user maintains 12-18 identities Number of phishing and pharming sites grew over 1600% over the past year Corporate IT Ops manage an average of 73 applications and 46 suppliers, often with individual directories Regulators are becoming stricter about compliance and auditing Orphaned accounts and identities lead to security problems Source: Microsoft’s internal research and Anti-phishing Working Group Feb 2005
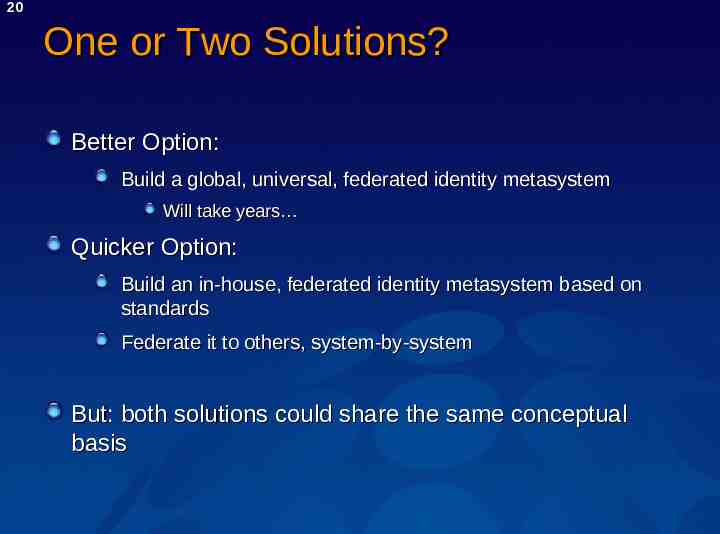
20 One or Two Solutions? Better Option: Build a global, universal, federated identity metasystem Will take years Quicker Option: Build an in-house, federated identity metasystem based on standards Federate it to others, system-by-system But: both solutions could share the same conceptual basis
21 Identity Laws and Metasystem
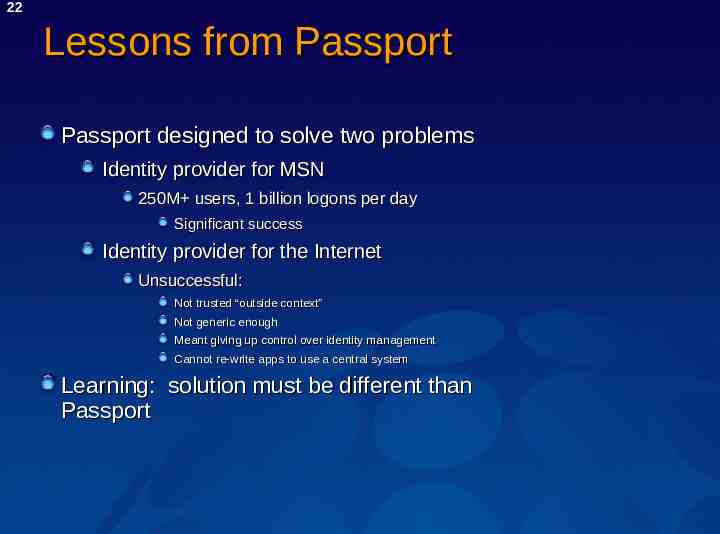
22 Lessons from Passport Passport designed to solve two problems Identity provider for MSN 250M users, 1 billion logons per day Significant success Identity provider for the Internet Unsuccessful: Not trusted “outside context” Not generic enough Meant giving up control over identity management Cannot re-write apps to use a central system Learning: solution must be different than Passport
23 Idea of an Identity Metasystem Not an Identity System Agreement on metadata and protocols, allowing multiple identity providers and brokers Based on open standards Supported by multiple technologies and platforms Adhering to Laws of Identity With full respect of privacy needs
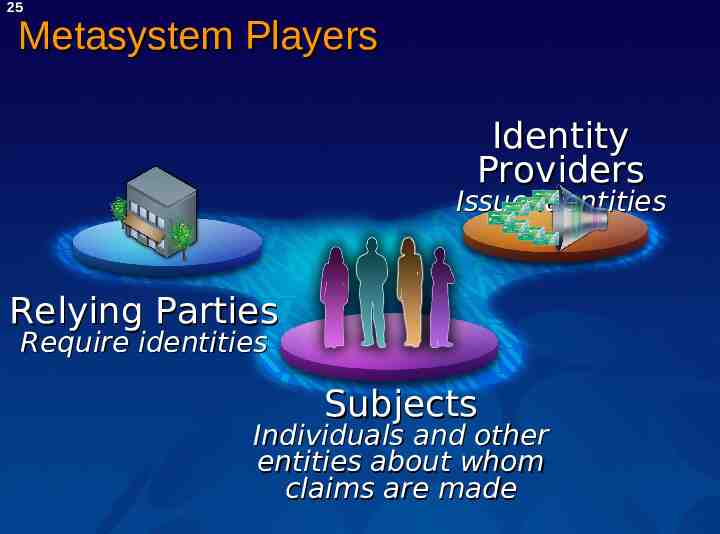
24 Roles Within Identity Metasystem Identity Providers Organisations, governments, even end-users They provide Identity Claims about a Subject Name, vehicles allowed to drive, age, etc. Relying Parties Online services or sites, doors, etc. Subjects Individuals and other bodies that need its identity established
25 Metasystem Players Identity Providers Issue identities Relying Parties Require identities Subjects Individuals and other entities about whom claims are made
26 Identity Metasystem Today Basically, the set of WS-* Security Guidelines as we have it Plus Software that implements the services Microsoft and many others working on it Companies that would use it Still to come, but early adopters exist End-users that would trust it Will take time
27 Identity Lawswww.identityblog.com 1. 2. User Control and Consent Minimal Disclosure for a Constrained Use 3. Justifiable Parties 4. Directed Identity 5. Pluralism of Operators and Technologies 6. Human Integration 7. Consistent Experience Across Contexts
28 Enterprise Applicability That proposed metasystem would work well inside a corporation But, it will be 5-7 years at least before the beginning of adoption! Of course, we need a solution before it becomes a reality Following the principles seems a good idea while planning immediate solutions Organic growth likely to lead to an identity metasystem in long term
29 Enterprise Trends Kerberos can no longer easily span disconnected identity forests and technologies We are moving away from Groups and traditional ACLs Increasingly limited and difficult to manage on large scales towards a combination of: Role-Based Access Management, and, Rich Claims Authorization PKI is still too restrictive, but it is clearly a component of a possible solution
30 Components and Terminology
31 What is Identity Management? o rd w s s a P ent m e g Mana ign S e l Sing On Fede ratio n Secure Remote Access Role Manageme nt Provisionin g Web Services Security g& n i t i d Au ing t r o p Re Authorization Digital Rights ntt Manageme Managemen g Stron tion i ca t n e h Aut ies r o t c Dire PKI
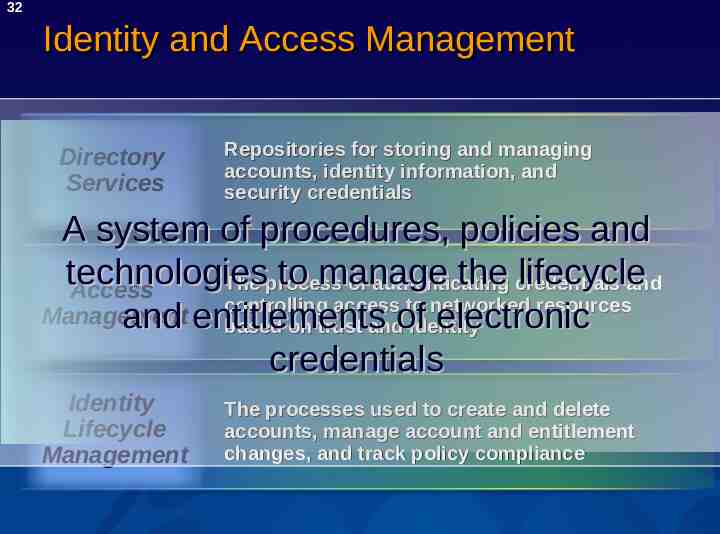
32 Identity and Access Management Directory Services Repositories for storing and managing accounts, identity information, and security credentials A system of procedures, policies and technologies to manage the credentials lifecycle The process of authenticating and Access controlling access to networked resources Management and entitlements electronic based on trust andof identity credentials Identity Lifecycle Management The processes used to create and delete accounts, manage account and entitlement changes, and track policy compliance
33 Remember the Chaos? Enterprise Directory Authenticati Authorizatio on Identity n Data Authenticati Authorizatio on Identity n Data Authenticati Authorizatio on Identity n Data Authenticati Authorizatio on Identity n Data Authenticati Authorizatio on Identity n Data Authenticati Authorizatio on Identity n Data Authenticati Authorizatio on Identity n Data HR System NOS Lotus Notes Apps Infra Application COTS Application In-House Application In-House Application
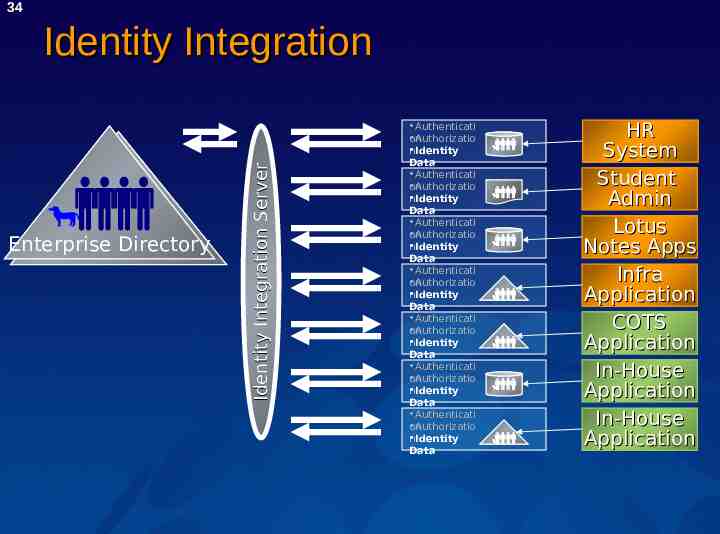
34 Enterprise Directory Identity Integration Server Identity Integration Authenticati Authorizatio on Identity n Data Authenticati Authorizatio on Identity n Data Authenticati Authorizatio on Identity n Data Authenticati Authorizatio on Identity n Data Authenticati Authorizatio on Identity n Data Authenticati Authorizatio on Identity n Data Authenticati Authorizatio on Identity n Data HR System Student Admin Lotus Notes Apps Infra Application COTS Application In-House Application In-House Application
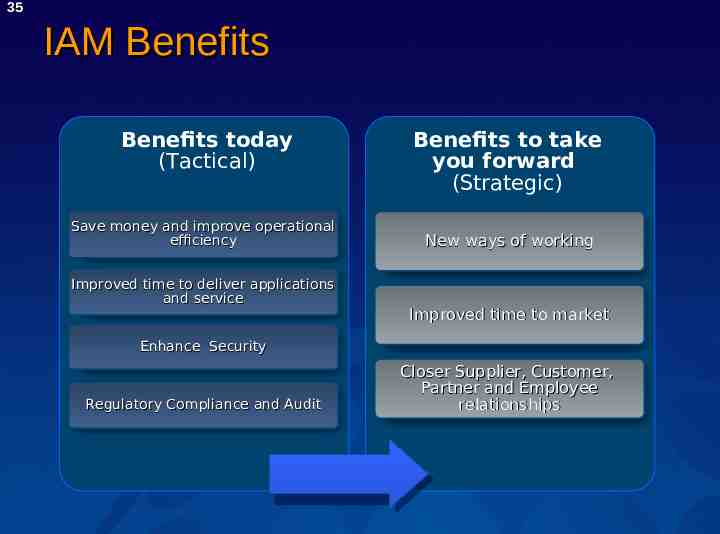
35 IAM Benefits Benefits today (Tactical) Save money and improve operational efficiency Improved time to deliver applications and service Benefits to take you forward (Strategic) New ways of working Improved time to market Enhance Security Regulatory Compliance and Audit Closer Supplier, Customer, Partner and Employee relationships
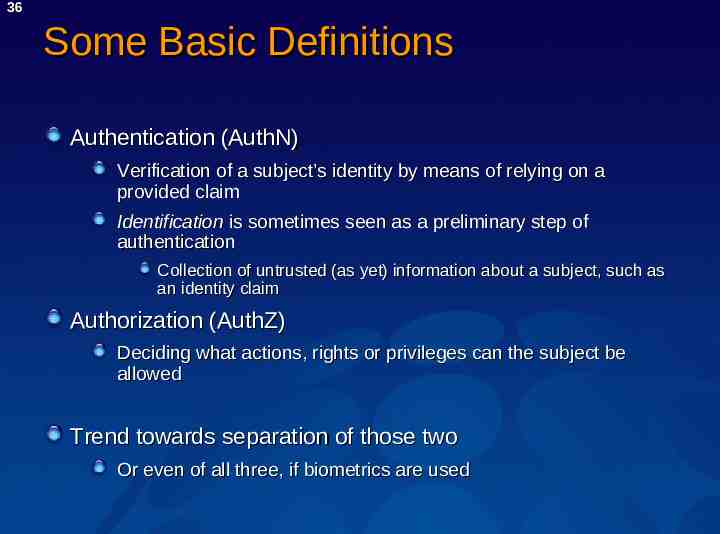
36 Some Basic Definitions Authentication (AuthN) Verification of a subject’s identity by means of relying on a provided claim Identification is sometimes seen as a preliminary step of authentication Collection of untrusted (as yet) information about a subject, such as an identity claim Authorization (AuthZ) Deciding what actions, rights or privileges can the subject be allowed Trend towards separation of those two Or even of all three, if biometrics are used
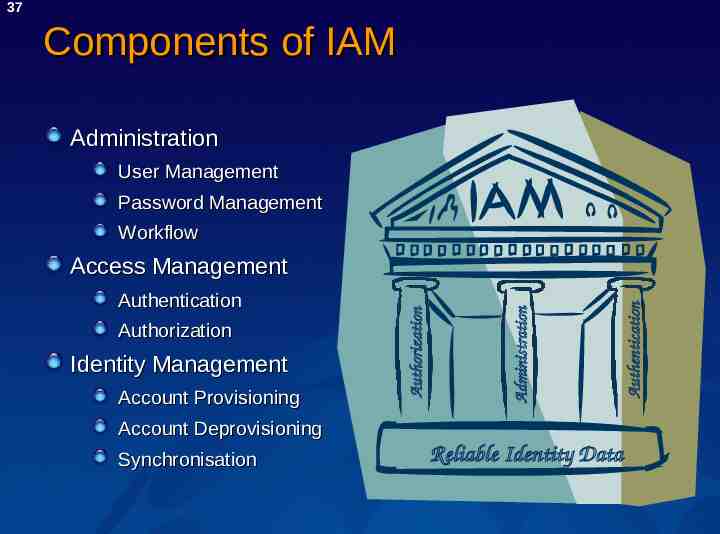
37 Components of IAM Administration User Management Password Management Workflow Identity Management Account Provisioning Account Deprovisioning Synchronisation Reliable Identity Data Authentication Authorization Administration Authentication Authorization Access Management
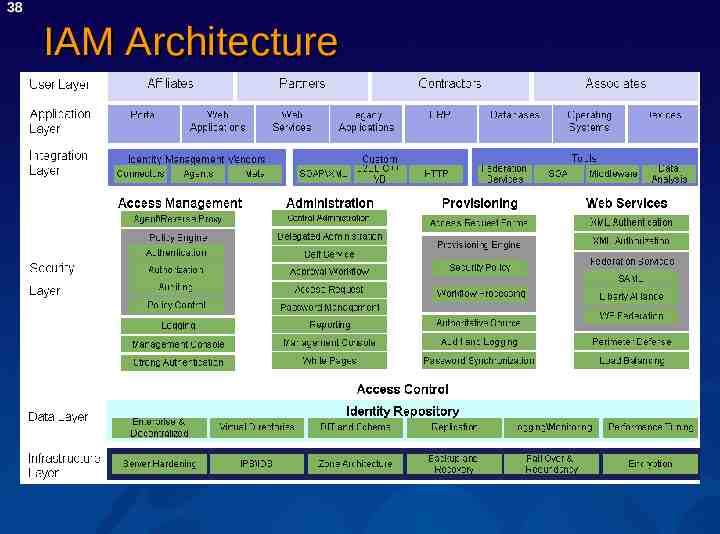
38 IAM Architecture
39 Roadmap
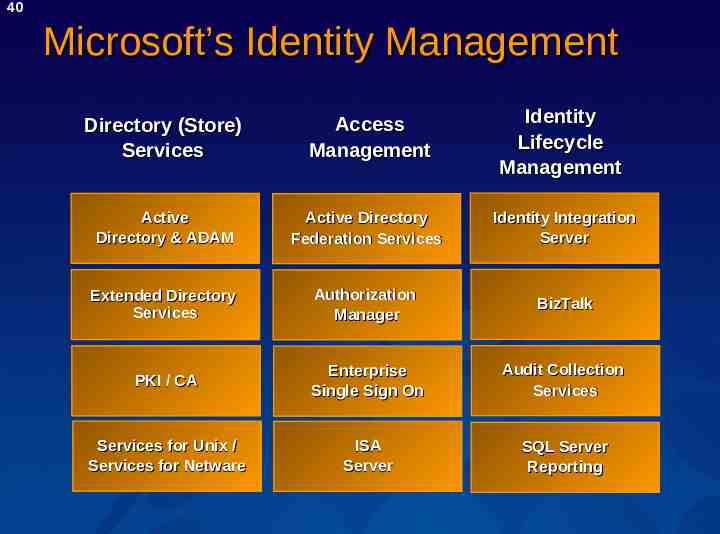
40 Microsoft’s Identity Management Directory (Store) Services Access Management Identity Lifecycle Management Active Directory & ADAM Active Directory Federation Services Identity Integration Server Extended Directory Services Authorization Manager BizTalk PKI / CA Enterprise Single Sign On Audit Collection Services Services for Unix / Services for Netware ISA Server SQL Server Reporting
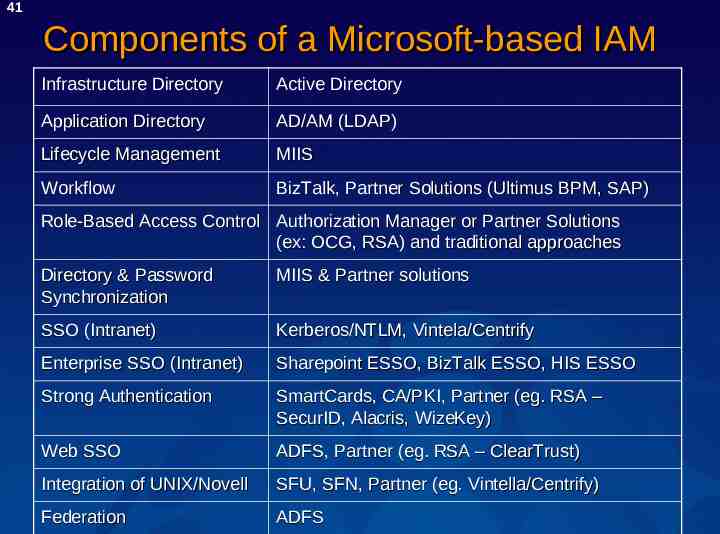
41 Components of a Microsoft-based IAM Infrastructure Directory Active Directory Application Directory AD/AM (LDAP) Lifecycle Management MIIS Workflow BizTalk, Partner Solutions (Ultimus BPM, SAP) Role-Based Access Control Authorization Manager or Partner Solutions (ex: OCG, RSA) and traditional approaches Directory & Password Synchronization MIIS & Partner solutions SSO (Intranet) Kerberos/NTLM, Vintela/Centrify Enterprise SSO (Intranet) Sharepoint ESSO, BizTalk ESSO, HIS ESSO Strong Authentication SmartCards, CA/PKI, Partner (eg. RSA – SecurID, Alacris, WizeKey) Web SSO ADFS, Partner (eg. RSA – ClearTrust) Integration of UNIX/Novell SFU, SFN, Partner (eg. Vintella/Centrify) Federation ADFS
42 Summary
43 Summary We have reached an “Identity Crisis” both on the intranet and the Internet Identity Metasystem suggests a unifying way forward Meanwhile, Identity and Access Management systems need to be built so enterprises can benefit immediately Microsoft is rapidly becoming a strong provider of IAM technologies and IM vision www.microsoft.com/idm & www.microsoft.com/itsshowtime & www.microsoft.com/technet
44 Special Thanks This seminar was prepared with the help of: Oxford Computer Group Ltd Expertise in Identity and Access Management (Microsoft Partner) IT Service Delivery and Training www.oxfordcomputergroup.com Microsoft, with special thanks to: Daniel Meyer – thanks for many slides Steven Adler, Ronny Bjones, Olga Londer – planning and reviewing Philippe Lemmens, Detlef Eckert – Sponsorship Bas Paumen & NGN - feedback