Developing and Securing the Cloud Dr. Bhavani Thuraisingham The
11 Slides311.50 KB
Developing and Securing the Cloud Dr. Bhavani Thuraisingham The University of Texas at Dallas Introduction to the Course January – May 2015
Objective of the Unit This unit provides an overview of the course. The course describes concepts, developments, challenges, and directions in - Secure Web Services - Secure Cloud Computing Book: Bhavani Thuraisingham, Developing and Securing the Cloud, CRC Press, November 2013
Outline of the Unit Outline of Course Course Work Course Rules Contact Papers to read for lectures after Spring Break Index to lectures and preparation for exams Acknowledgement: - AFOSR for funding our research in assured cloud computing - NSF for funding our capacity building effort in cloud computing
Course Work Two exams each worth 25 points Programming project worth 20 points Two homework assignments – 7 points each Two term papers – 8 points each Programming Project Exams
Course Rules Course attendance is mandatory; unless permission is obtained from instructor for missing a class with a valid reason (documentation needed for medical emergency for student or a close family member – e.g., spouse, parent, child). Attendance will be collected every lecture. 3 points will be deducted out of 100 for each lecture missed without approval. Each student will work individually Late assignments will not be accepted. All assignments have to be turned in just after the lecture on the due date No make up exams unless student can produce a medical certificate or give evidence of close family emergency Copying material from other sources will not be permitted unless the source is properly referenced Any student who plagiarizes from other sources will be reported to the appropriate UTD authroities
Contact For more information please contact - Dr. Bhavani Thuraisingham - Professor of Computer Science and - Director of Cyber Security Research Center Erik Jonsson School of Engineering and Computer Science EC31, The University of Texas at Dallas Richardson, TX 75080 - Phone: 972-883-4738 - Fax: 972-883-2399 - Email: [email protected] - URL:http://www.utdallas.edu/ bxt043000/
Term Paper Any topic we have discussed in class (e.g., web services, identity management, secure cloud, secure cloud query processing, ) Survey different approaches Give your analysis of the approaches Organization - Abstract - Approaches - Analysis - Conclusion - References
Programming Project Any topic related to cloud security and implement Learn the Hadoop/MapReduce Framework Example - Query modification in the cloud - Secure information sharing in the cloud - Secure social network in the cloud - Email filtering in the cloud
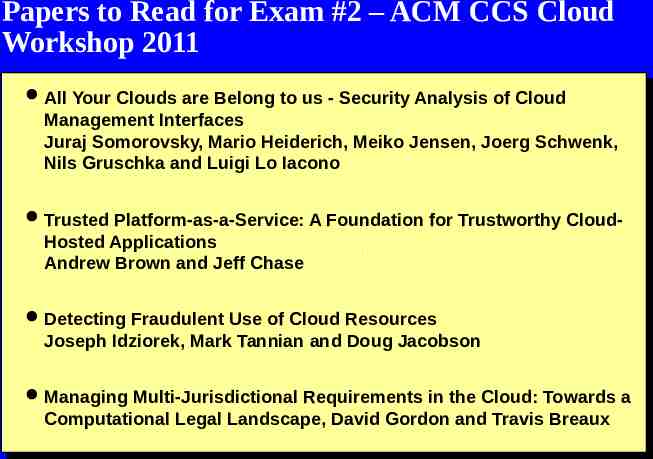
Papers to Read for Exam #2 – ACM CCS Cloud Workshop 2011 All Your Clouds are Belong to us - Security Analysis of Cloud Management Interfaces Juraj Somorovsky, Mario Heiderich, Meiko Jensen, Joerg Schwenk, Nils Gruschka and Luigi Lo Iacono Trusted Platform-as-a-Service: A Foundation for Trustworthy Cloud- Hosted Applications Andrew Brown and Jeff Chase Detecting Fraudulent Use of Cloud Resources Joseph Idziorek, Mark Tannian and Doug Jacobson Managing Multi-Jurisdictional Requirements in the Cloud: Towards a Computational Legal Landscape, David Gordon and Travis Breaux
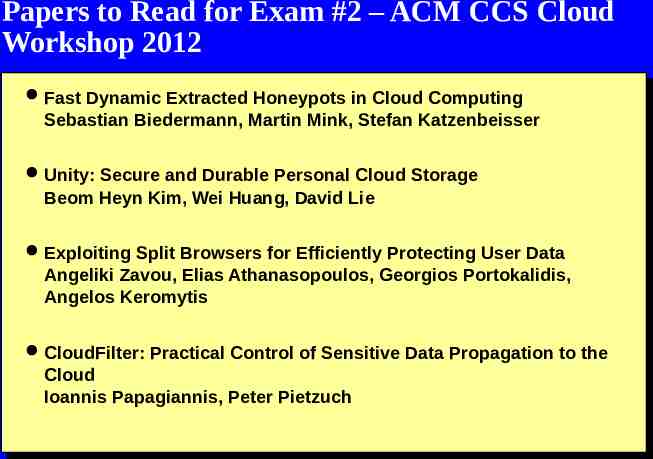
Papers to Read for Exam #2 – ACM CCS Cloud Workshop 2012 Fast Dynamic Extracted Honeypots in Cloud Computing Sebastian Biedermann, Martin Mink, Stefan Katzenbeisser Unity: Secure and Durable Personal Cloud Storage Beom Heyn Kim, Wei Huang, David Lie Exploiting Split Browsers for Efficiently Protecting User Data Angeliki Zavou, Elias Athanasopoulos, Georgios Portokalidis, Angelos Keromytis CloudFilter: Practical Control of Sensitive Data Propagation to the Cloud Ioannis Papagiannis, Peter Pietzuch
Papers to Read for Exam #2 – ACM CCS Cloud Workshop 2013 Structural Cloud Audits that Protect Private Information Hongda Xiao; Bryan Ford; Joan Feigenbaum Cloudoscopy: Services Discovery and Topology Mapping Amir Herzberg; Haya Shulman; Johanna Ullrich; Edgar Weippl Cloudsweeper: Enabling Data-Centric Document Management for Secure Cloud Archives Chris Kanich; Peter Snyder In addition, the following paper from IEEE S&P Symposium Yangchun Fu, Zhiqiang Lin: Space Traveling across VM: Automatically Bridging the Semantic Gap in Virtual Machine Introspection via Online Kernel Data Redirection. IEEE Symposium on Security and Privacy 2012: 586-600