Cellular Networks Wireless Networks Spring 2005
58 Slides516.50 KB
Cellular Networks Wireless Networks Spring 2005
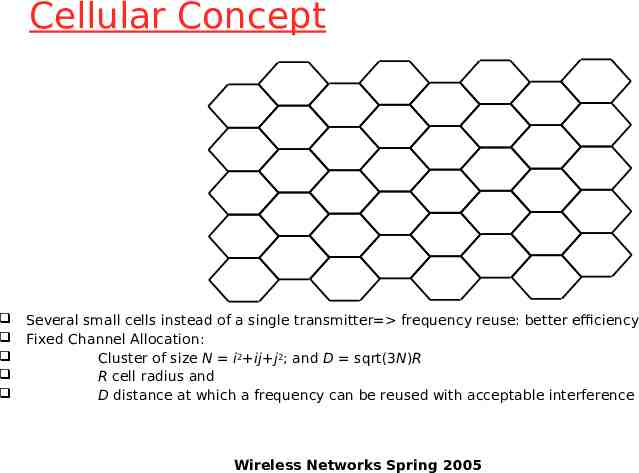
Cellular Network Organization Use multiple low-power transmitters (100 W or less) Areas divided into cells o Each served by its own antenna o Served by base station consisting of transmitter, receiver, and control unit o Band of frequencies allocated o Cells set up such that antennas of all neighbors are equidistant (hexagonal pattern) Wireless Networks Spring 2005
Frequency Reuse Adjacent cells assigned different frequencies to avoid interference or crosstalk Objective is to reuse frequency in nearby cells o 10 to 50 frequencies assigned to each cell o Transmission power controlled to limit power at that frequency escaping to adjacent cells o The issue is to determine how many cells must intervene between two cells using the same frequency Wireless Networks Spring 2005
Cellular Concept Several small cells instead of a single transmitter frequency reuse: better efficiency Fixed Channel Allocation: Cluster of size N i2 ij j2; and D sqrt(3N)R R cell radius and D distance at which a frequency can be reused with acceptable interference Wireless Networks Spring 2005
Examples Wireless Networks Spring 2005
Approaches to Cope with Increasing Capacity Adding new channels Frequency borrowing – frequencies are taken from adjacent cells by congested cells Cell splitting – cells in areas of high usage can be split into smaller cells Cell sectoring – cells are divided into a number of wedge-shaped sectors, each with their own set of channels Microcells – antennas move to buildings, hills, and lamp posts Wireless Networks Spring 2005
Cellular System Overview Wireless Networks Spring 2005
Cellular Systems Terms Base Station (BS) – includes an antenna, a controller, and a number of receivers Mobile telecommunications switching office (MTSO) – connects calls between mobile units Two types of channels available between mobile unit and BS o Control channels – used to exchange information having to do with setting up and maintaining calls o Traffic channels – carry voice or data connection between users Wireless Networks Spring 2005
Steps in an MTSO Controlled Call between Mobile Users Mobile unit initialization Mobile-originated call Paging Call accepted Ongoing call Handoff Wireless Networks Spring 2005
Additional Functions in an MTSO Controlled Call Call blocking Call termination Call drop Calls to/from fixed and remote mobile subscriber Wireless Networks Spring 2005
Mobile Radio Propagation Effects Signal strength o Must be strong enough between base station and mobile unit to maintain signal quality at the receiver o Must not be so strong as to create too much cochannel interference with channels in another cell using the same frequency band Fading o Signal propagation effects may disrupt the signal and cause errors Wireless Networks Spring 2005
Handoff Performance Metrics Cell blocking probability – probability of a new call being blocked Call dropping probability – probability that a call is terminated due to a handoff Call completion probability – probability that an admitted call is not dropped before it terminates Probability of unsuccessful handoff – probability that a handoff is executed while the reception conditions are inadequate Wireless Networks Spring 2005
Handoff Performance Metrics Handoff blocking probability – probability that a handoff cannot be successfully completed Handoff probability – probability that a handoff occurs before call termination Rate of handoff – number of handoffs per unit time Interruption duration – duration of time during a handoff in which a mobile is not connected to either base station Handoff delay – distance the mobile moves from the point at which the handoff should occur to the point at which it does occur Wireless Networks Spring 2005
Handoff Strategies Used to Determine Instant of Handoff Relative signal strength Relative signal strength with threshold Relative signal strength with hysteresis Relative signal strength with hysteresis and threshold Prediction techniques Wireless Networks Spring 2005
Power Control Design issues making it desirable to include dynamic power control in a cellular system o Received power must be sufficiently above the background noise for effective communication o Desirable to minimize power in the transmitted signal from the mobile Reduce cochannel interference, alleviate health concerns, save battery power o In SS systems using CDMA, it’s desirable to equalize the received power level from all mobile units at the BS Wireless Networks Spring 2005
Types of Power Control Open-loop power control o Depends solely on mobile unit o No feedback from BS o Not as accurate as closed-loop, but can react quicker to fluctuations in signal strength Closed-loop power control o Adjusts signal strength in reverse channel based on metric of performance o BS makes power adjustment decision and communicates to mobile on control channel Wireless Networks Spring 2005
Traffic Engineering Ideally, available channels would equal number of subscribers active at one time In practice, not feasible to have capacity handle all possible load For N simultaneous user capacity and L subscribers o L N – nonblocking system o L N – blocking system Wireless Networks Spring 2005
Blocking System Performance Questions Probability that call request is blocked? What capacity is needed to achieve a certain upper bound on probability of blocking? What is the average delay? What capacity is needed to achieve a certain average delay? Wireless Networks Spring 2005
Traffic Intensity Load presented to a system: A λh mean rate of calls attempted per unit time h mean holding time per successful call A average number of calls arriving during average holding period Wireless Networks Spring 2005
Capacity in Cellular Systems Blocking Probability (Grade Of Service): Erlang B formula GOS AC / C! C n A n 0 / n! Based on the above formula, we can determine the minimum N needed to support a desired grade of service. Wireless Networks Spring 2005
Factors that Determine the Nature of the Traffic Model Manner in which blocked calls are handled o Lost calls delayed (LCD) – blocked calls put in a queue awaiting a free channel o Blocked calls rejected and dropped Lost calls cleared (LCC) – user waits before another attempt Lost calls held (LCH) – user repeatedly attempts calling Number of traffic sources o Whether number of users is assumed to be finite or infinite Wireless Networks Spring 2005
First-Generation Analog Advanced Mobile Phone Service (AMPS) o In North America, two 25-MHz bands allocated to AMPS One for transmission from base to mobile unit One for transmission from mobile unit to base o Each band split in two to encourage competition (12.5MHz per operator) o Channels of 30 KHz: 21 control channels (FSK), 395 traffic channels (FM voice) per operator o Frequency reuse exploited (R 7) Wireless Networks Spring 2005
AMPS Operation Subscriber initiates call by keying in phone number and presses send key MTSO verifies number and authorizes user MTSO issues message to user’s cell phone indicating send and receive traffic channels MTSO sends ringing signal to called party Party answers; MTSO establishes circuit and initiates billing information Either party hangs up; MTSO releases circuit, frees channels, completes billing Wireless Networks Spring 2005
Differences Between First and Second Generation Systems Digital traffic channels – first-generation systems are almost purely analog; second-generation systems are digital Encryption – all second generation systems provide encryption to prevent eavesdropping Error detection and correction – secondgeneration digital traffic allows for detection and correction, giving clear voice reception Channel access – second-generation systems allow channels to be dynamically shared by a number of users Wireless Networks Spring 2005
TDMA Design Considerations Number of logical channels per physical channel (number of time slots in TDMA frame): 8 Maximum cell radius (R): 35 km Frequency: region around 900 MHz Maximum vehicle speed (Vm):250 km/hr Maximum coding delay: approx. 20 ms Maximum delay spread ( m): 10 s Bandwidth: Not to exceed 200 kHz (25 kHz per channel) Wireless Networks Spring 2005
GSM Network Architecture
Architecture of the GSM system Several providers setup mobile networks following the GSM standard within each country Components o o o o MS (mobile station) BS (base station) MSC (mobile switching center) LR (location register) Subsystems o RSS (radio subsystem): covers all radio aspects Base station subsystem o NSS (network and switching subsystem): call forwarding, handover, switching o OSS (operation subsystem): management of the network Wireless Networks Spring 2005
GSM: elements and interfaces radio cell MS BSS MS Um radio cell MS BTS RSS BTS Abis BSC BSC A MSC NSS MSC VLR signaling VLR HLR GMSC ISDN, PSTN IWF O OSS EIR AUC OMC Wireless Networks Spring 2005 PDN
GSM: system architecture radio subsyste m MS MS network and switching subsystem BTS Abis BSC EIR SS7 BTS ISDN PSTN MSC Um HLR VLR BTS BTS Fixed partner networks BSC BSS A MSC IWF ISDN PSTN PDN Wireless Networks Spring 2005
Radio subsystem Components radio subsystem MS network and switching subsystem MS BTS (Base Transceiver Station): sender and receiver BSC (Base Station Controller): controlling several transceivers Um BTS BTS BTS Abis BSC BSC BTS BSS o MS (Mobile Station) o BSS (Base Station Subsystem): consisting of MSC A MSC Interfaces o Um : radio interface o Abis : standardized, open interface with 16 kbit/s user channels o A: standardized, open interface with 64 kbit/s user channels Wireless Networks Spring 2005
Mobile Station Mobile station communicates across Um interface (air interface) with base station transceiver in same cell as mobile unit Mobile equipment (ME) – physical terminal, such as a telephone or PDA o ME includes radio transceiver, digital signal processors and subscriber identity module (SIM) GSM subscriber units are generic until SIM is inserted o SIMs roam, not necessarily the subscriber devices Wireless Networks Spring 2005
Base Station Subsystem (BSS) BSS consists of base station controller and one or more base transceiver stations (BTS) Each BTS defines a single cell o Includes radio antenna, radio transceiver and a link to a base station controller (BSC) BSC reserves radio frequencies, manages handoff of mobile unit from one cell to another within BSS, and controls paging Wireless Networks Spring 2005
Network and switching subsystem network subsystem fixed partner networks ISDN PSTN MSC SS7 MSC (Mobile Services Switching Center): IWF (Interworking Functions) EIR HLR ISDN (Integrated Services Digital Network) PSTN (Public Switched Telephone Network) PSPDN (Packet Switched Public Data Net.) CSPDN (Circuit Switched Public Data Net.) Databases VLR MSC IWF Components ISDN PSTN PSPDN CSPD N HLR (Home Location Register) VLR (Visitor Location Register) EIR (Equipment Identity Register) Wireless Networks Spring 2005
Network Subsystem (NS) Provides link between cellular network and PSTNs Controls handoffs between cells in different BSSs Authenticates users and validates accounts Enables worldwide roaming of mobile users Central element of NS is the mobile switching center (MSC) Wireless Networks Spring 2005
Mobile Switching Center (MSC) Databases Home location register (HLR) database – stores information about each subscriber that belongs to it Visitor location register (VLR) database – maintains information about subscribers currently physically in the region Authentication center database (AuC) – used for authentication activities, holds encryption keys Equipment identity register database (EIR) – keeps track of the type of equipment that exists at the mobile station Wireless Networks Spring 2005
TDMA Format – Time Slot Fields Trail bits – allow synchronization of transmissions from mobile units located at different distances Encrypted bits – encrypted data Stealing bit - indicates whether block contains data or is "stolen" Training sequence – used to adapt parameters of receiver to the current path propagation characteristics o Strongest signal selected in case of multipath propagation Guard bits – used to avoid overlapping with other bursts Wireless Networks Spring 2005
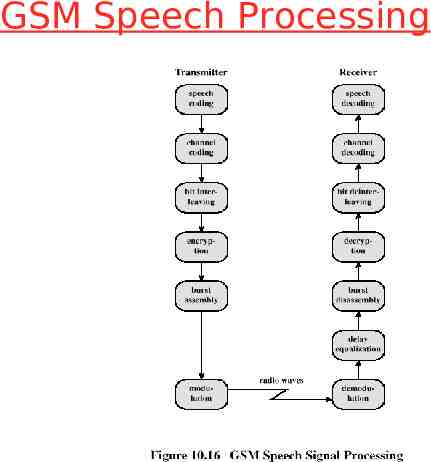
GSM Speech Processing
GSM Speech Processing Steps Speech compressed using a predictive coding scheme Divided into blocks, each of which is protected partly by CRC and partly by a convolutional code Interleaving to protect against burst errors Encryption for providing privacy Assembled into time slots Modulated for analog transmission using FSK Wireless Networks Spring 2005
GSM Signaling Protocol
Functions Provided by Protocols Protocols above the link layer of the GSM signaling protocol architecture provide specific functions: o o o o o Radio resource management Mobility management Connection management Mobile application part (MAP) BTS management Wireless Networks Spring 2005
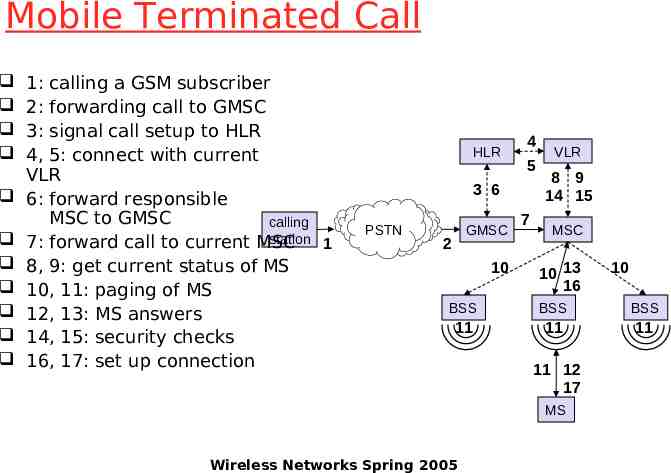
Mobile Terminated Call 1: calling a GSM subscriber 2: forwarding call to GMSC 3: signal call setup to HLR 4, 5: connect with current VLR 6: forward responsible MSC to GMSC calling station 1 7: forward call to current MSC 8, 9: get current status of MS 10, 11: paging of MS 12, 13: MS answers 14, 15: security checks 16, 17: set up connection HLR 4 5 3 6 PSTN GMSC 2 10 7 VLR 8 9 14 15 MSC 10 13 16 10 BSS BSS BSS 11 11 11 11 12 17 MS Wireless Networks Spring 2005
Mobile Originated Call 1, 2: connection request 3, 4: security check 5-8: check resources (free circuit) 9-10: set up call VLR 3 4 PSTN 6 5 GMSC 7 8 2 9 MS Wireless Networks Spring 2005 MSC 1 10 BSS
MTC/MOC MS BTS MTC MS MOC BTS paging request channel request channel request immediate assignment immediate assignment paging response service request authentication request authentication request authentication response authentication response ciphering command ciphering command ciphering complete ciphering complete setup setup call confirmed call confirmed assignment command assignment command assignment complete assignment complete alerting alerting connect connect connect acknowledge connect acknowledge data/speech exchange data/speech exchange Wireless Networks Spring 2005
4 types of handover 1 MS BTS 2 3 4 MS MS MS BTS BTS BTS BSC BSC BSC MSC MSC Wireless Networks Spring 2005
Handover decision receive level BTSold receive level BTSold HO MARGIN MS MS BTSold BTSnew Wireless Networks Spring 2005
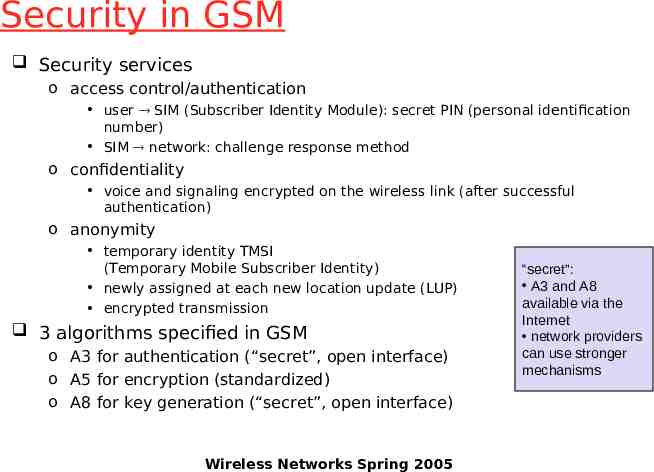
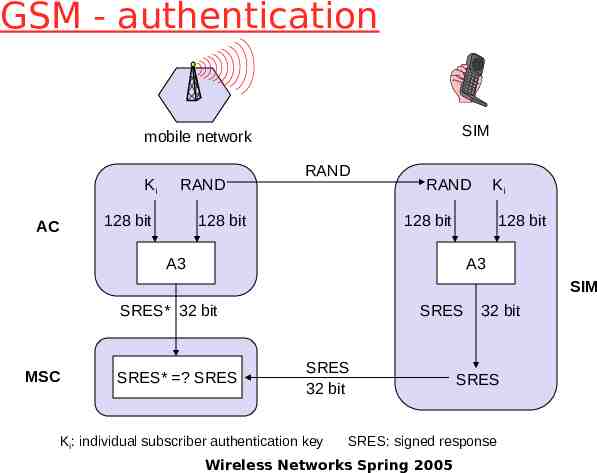
Security in GSM Security services o access control/authentication user SIM (Subscriber Identity Module): secret PIN (personal identification number) SIM network: challenge response method o confidentiality voice and signaling encrypted on the wireless link (after successful authentication) o anonymity temporary identity TMSI (Temporary Mobile Subscriber Identity) newly assigned at each new location update (LUP) encrypted transmission 3 algorithms specified in GSM o A3 for authentication (“secret”, open interface) o A5 for encryption (standardized) o A8 for key generation (“secret”, open interface) Wireless Networks Spring 2005 “secret”: A3 and A8 available via the Internet network providers can use stronger mechanisms
GSM - authentication SIM mobile network Ki RAND 128 bit AC RAND 128 bit RAND Ki 128 bit 128 bit A3 A3 SIM SRES* 32 bit MSC SRES* ? SRES SRES SRES 32 bit Ki: individual subscriber authentication key 32 bit SRES SRES: signed response Wireless Networks Spring 2005
GSM - key generation and encryption MS with SIM mobile network (BTS) Ki AC RAND 128 bit RAND 128 bit RAND 128 bit A8 cipher key BTS Ki 128 bit SIM A8 Kc 64 bit Kc 64 bit data encrypted data A5 SRES data MS A5 Wireless Networks Spring 2005
IS-95 (CdmaOne) IS-95: standard for the radio interface IS-41: standard for the network part Operates in 800MHz and 1900MHz bands Uses DS-CDMA technology (1.2288 Mchips/s) Forward link (downlink): (2,1,9)-convolutional code, interleaved, 64 chips spreading sequence (Walsh-Hadamard functions) Pilot channel, synchronization channel, 7 paging channels, up to 63 traffic channels Reverse link (uplink): (3,1,9)-convolutional code, interleaved, 6 bits are mapped into a Walsh-Hadamard sequence, spreading using a user-specific code Tight power control (open-loop, fast closed loop) Wireless Networks Spring 2005
Advantages of CDMA Cellular Frequency diversity – frequency-dependent transmission impairments have less effect on signal Multipath resistance – chipping codes used for CDMA exhibit low cross correlation and low autocorrelation Privacy – privacy is inherent since spread spectrum is obtained by use of noise-like signals Graceful degradation – system only gradually degrades as more users access the system Wireless Networks Spring 2005
Drawbacks of CDMA Cellular Self-jamming – arriving transmissions from multiple users not aligned on chip boundaries unless users are perfectly synchronized Near-far problem – signals closer to the receiver are received with less attenuation than signals farther away Soft handoff – requires that the mobile acquires the new cell before it relinquishes the old; this is more complex than hard handoff used in FDMA and TDMA schemes Wireless Networks Spring 2005
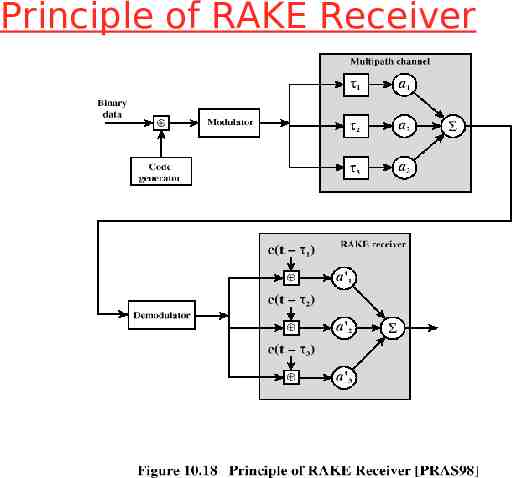
CDMA Design Considerations RAKE receiver – when multiple versions of a signal arrive more than one chip interval apart, RAKE receiver attempts to recover signals from multiple paths and combine them o This method achieves better performance than simply recovering dominant signal and treating remaining signals as noise Soft Handoff – mobile station temporarily connected to more than one base station simultaneously Wireless Networks Spring 2005
Principle of RAKE Receiver
Forward Link Channels Pilot: allows the mobile unit to acquire timing information, provides phase reference and provides means for signal strength comparison Synchronization: used by mobile station to obtain identification information about cellular system Paging: contain messages for one or more mobile stations Traffic: the forward channel supports 55 traffic channels Wireless Networks Spring 2005
Forward Traffic Processing Steps Speech is encoded at a rate of 8550 bps Additional bits added for error detection Data transmitted in 2-ms blocks with forward error correction provided by a convolutional encoder Data interleaved in blocks to reduce effects of errors Data bits are scrambled, serving as a privacy mask o Using a long code based on user’s electronic serial number Wireless Networks Spring 2005
Forward Traffic Processing Steps Power control information inserted into traffic channel DS-SS function spreads the 19.2 kbps to a rate of 1.2288 Mbps using one row of 64 x 64 Walsh matrix Digital bit stream modulated onto the carrier using QPSK modulation scheme Wireless Networks Spring 2005
Reverse Traffic Processing Steps Convolutional encoder at rate 1/3 Spread the data using a Walsh matrix o Use a 6-bit piece of data as an index to the Walsh matrix o To improve reception at base station Data burst randomizer Spreading using the user-specific long code mask Wireless Networks Spring 2005
Third-Generation Capabilities Voice quality comparable to the public switched telephone network 144 kbps data rate available to users in highspeed motor vehicles over large areas 384 kbps available to pedestrians standing or moving slowly over small areas Support for 2.048 Mbps for office use Symmetrical/asymmetrical data transmission rates Support for both packet switched and circuit switched data services Wireless Networks Spring 2005