ADVANCED FUNCTIONALITY & TROUBLESHOOTING
48 Slides2.76 MB
ADVANCED FUNCTIONALITY & TROUBLESHOOTING
Agenda Internet Shield Architecture Advanced functionality IDS vs. packet filter Stateful packet filters Dynamic firewall rules Cisco Network Admission Control (NAC) Troubleshooting Troubleshooting Internet Shield configurations Inspecting logfiles Page 2
PROCESSES AND SERVICES
AVCS Processes F-Secure Management Agent fameh32.exe, fch32.exe, fsih32.exe, fsnrb32.exe, fsm32.exe, fsma32.exe, fsmb32.exe, fsguidll.exe F-Secure Virus & Spy Protection fsav32.exe, fsaw.exe, fsgk32.exe, fsgk32st.exe, fsdfwd.exe, fsqh.exe, fsrw.exe, fssm32.exe F-Secure Automatic Update Agent fsbwsys.exe, F-Secure Automatic Update.exe Page 4
Processes: FSMA fsm32.exe F-Secure Manager, displays the F- tray icon fsma32.exe F-Secure Management Agent (Service) fsmb32.exe Message Broker, processes communication between different modules of the various products fsnrb32.exe Handles the communication between the hosts and the fameh32.exe forwarding Alert and Messaging Handler, handles alert and log fch32.exe Configuration Handler, reads the base policy files and the incremental policy files fsih32.exe installations the PMS writes Installation Handler. Launches ilaunchr.exe during Page 5
Processes: Virus & Spy Protection fsav32.exe Anti-Virus Handler fsaw.exe F-Secure Ad-Watch (Browser Control) fsdfwd.exe Anti-Virus Firewall Daemon. Redirects e-mails to the Scanner Manager (Service) fsqh.exe Handles object quarantine fsgk32.exe Gatekeeper Handler. Receives real-time scan requests from the Gatekeeper fsgk32st.exe Gatekeeper Handler Starter (Service) fsrw.exe F-Secure Reg-Watch (System Control) fssm32.exe Scanner Manager. Manages scanning engines Page 6
Virus & Spy Protection Services F-Secure Management Agent Environment NET STOP/START FSMA: fameh32.exe, fsaw.exe, fch32.exe, fsih32.exe, fnrb32.exe, fsm32.exe, fsma32.exe, fsmb32.exe, fsdfwd.exe, fsrw.exe, fsguidll.exe F-Secure Gatekeeper Environment NET STOP/START FSGKHS: fsgk32.exe, fsgk32st.exe, fssm32.exe F-Secure Automatic Update Environment NET STOP/START FSBWSYS: fsbwsys.exe, F-Secure Automatic Update.exe Page 7
INTERNET SHIELD ARCHITECTURE
Product Components DesktopF-Secure Manager Firewall Plug-ins Services User Interfaces Management Agent (FSMA) Firewall Daemon Email Scanning Module Dial-up Control API Hook Firewall Engine Kernel Packet Filter IDS Interceptor Page 9
Firewall Engine Fsdfw.sys Kernel mode component Firewall engine does the actual filtering based on rules Intrusion detection, packet filtering and application control are all done in Firewall Engine IDS handles the packets before packet filter TDI Driver is taking care of connection request filtering / checking which is needed for application control TCP "listen", TCP "connect", UDP "listen", UDP "sendto", RAWIP "create“ Page 10
Interceptor Fsndis5.sys Kernel mode component Loaded by Firewall Engine (fsdfw.sys) Intercepting network traffic in the NDIS layer Main purpose is to hook the network traffic and forward it to firewall engine Page 11
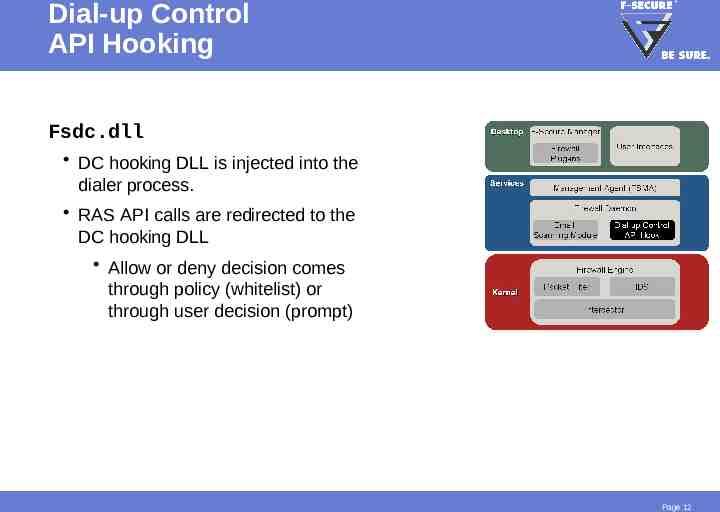
Dial-up Control API Hooking Fsdc.dll DC hooking DLL is injected into the dialer process. RAS API calls are redirected to the DC hooking DLL Allow or deny decision comes through policy (whitelist) or through user decision (prompt) Page 12
Firewall Daemon Fsdfwd.exe User mode component Receives alerts and status information directly from firewall engine Reads everything from policy tables Reads connection information received from TDI Driver Receives dial requests from the DC DLL and makes the decision to allow or deny the operation Sends firewall rules (filter) and IDS database to firewall engine Writes ACTION.LOG and DIAL.LOG Page 13
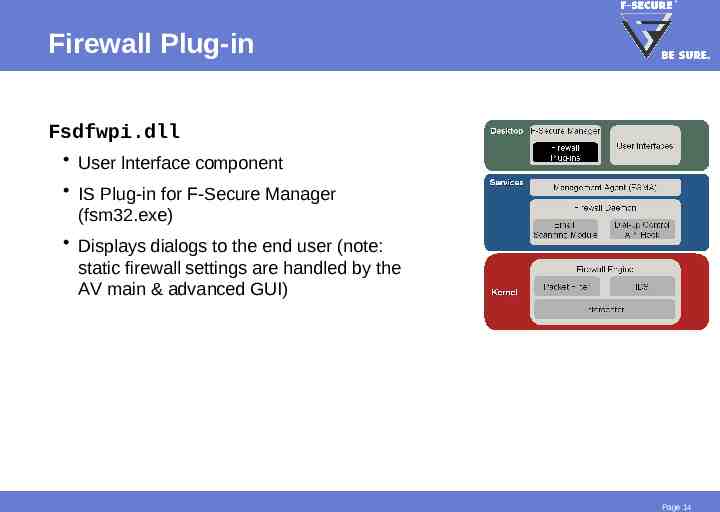
Firewall Plug-in Fsdfwpi.dll User lnterface component IS Plug-in for F-Secure Manager (fsm32.exe) Displays dialogs to the end user (note: static firewall settings are handled by the AV main & advanced GUI) Page 14
ADVANCED FUNCTIONALITY IDS VS. PACKET FILTER
Packet Filter Limitations Intrusion Detection Systems are becoming more and more popular Packet filters aren’t enough to secure the corporate networks While a firewall closes all unused ports, it cannot protect you from intentionally left open ports Closing all ports would affect the corporation’s operational requirements Example: A corporation leaves open TCP 80, so that HTTP traffic can reach the web server How can the firewall then protect the network against the countless HTTP based exploits This is where IDS comes in Page 16
The Anti-Virus for your Network Basically, IDS does for your network what Anti-Virus does for your file system IDS Solutions Signature based engines Pre-defined patterns tell the system, what type of network traffic most commonly correspond to an attack Heuristic engines The IDS learns over time, what patterns are considered normal for your network Pro: Doesn’t rely on signatures, able to detect unknown patterns Contra: Increasing number of false positives Page 17
Intrusion Detection System (IDS) IDS engine is divided in 3 parts Generic IP engine UDP protocol engine TCP protocol engine The system currently alerts on 31 malicous packets (13 IP, 5 UDP, 13 TCP) Database selected carefully to avoid false positives Page 18
Was that Really a Network Worm? Worm traffic Normal traffic Firewall Engine Header 1 TCP Port Packet Filter Payload None Header 2 IDS TCP Port Payload Worm Page 19
STATEFUL PACKET FILTERS
Stateful Packet Filter The firewall keeps a log of all open connections and the current state of all active connections Maintains a database of allowed and active IP based connections Uses the connection database to check if the datagram is part of an accepted connection Works for all IP Protocols (most common TCP, UDP and ICMP) Page 21
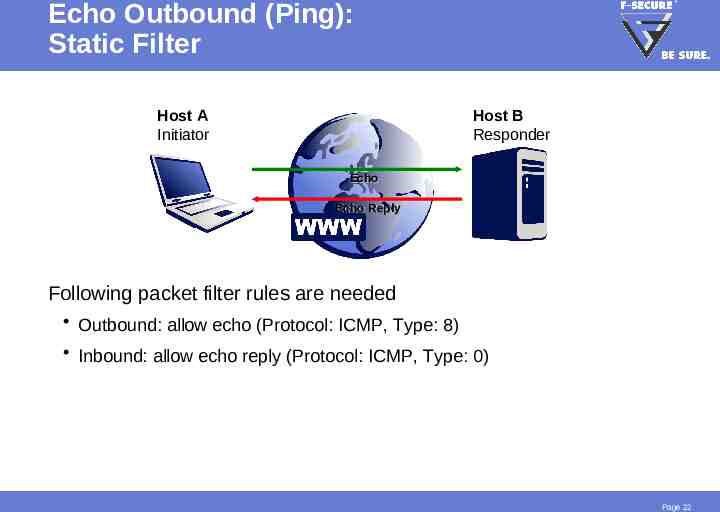
Echo Outbound (Ping): Static Filter Host A Initiator Host B Responder Echo Echo Reply Following packet filter rules are needed Outbound: allow echo (Protocol: ICMP, Type: 8) Inbound: allow echo reply (Protocol: ICMP, Type: 0) Page 22
Echo Outbound (Ping): Stateful Filter Host A Initiator Host B Responder Echo Echo Reply Listen ICMP, 0 Following packet filter rules are needed Outbound: allow echo (Protocol: ICMP, Type: 8) Page 23
APPLICATION CONTROL DYNAMIC FIREWALL RULES
Static Rules vs. Dynamic Rules The Internet Shield stateful packet filter works with two kinds of rules types Static rules Included in the pre-defined security levels or created by administrators Applied to domains or host via security levels (on PMC), always valid! Dynamic rules Created on the host at application launch (not related to security levels) Valid as long as the process is running Created only for server network applications opening a listening connection Page 25
Dynamic Firewall Rules Where to check them.? Dynamic firewall rules can only be viewed in the Policy Manager Console There is no reporting of such rules back to the Policy Manager Server The rules can be viewed from the local advanced user interface or in specific logfiles (fulldiag.htm) Static Rules Dynamic Rules Page 26
Firewall Dynamic Rules Placement Dynamic firewall rules are placed between the second last packet filter rule and the deny all rule The catch rule is not blocking inbound traffic, which matches one of many dynamic listening rules! Block unwanted inbound traffic with specific static rules! Page 27
Firewall Dynamic Rules Operation Host C 4 X 2Listen TCP 110 0.0.0.0/0 Host A Host B 3 1 POP3 Server Page 28
CISCO NETWORK ADMISSION CONTROL
System Components NAC is built from components of Cisco and various third party vendors (e.g. F-Secure) Cisco components Cisco Trust Agent (CTA) Cisco IOS Network Access Device (NAD) Access Control Server (ACS) F-Secure components CTA FS Plug-in ACS Policy Manager Console Cisco NAC support plug-in NAD Page 30
Cisco Trust Agent (CTA) One of the core components of the NAC system Must be installed on each client, whose policy state is to be validated before permitting network access Can be rolled out with PMC Checks Anti-Virus Client Security for the following posture validation attributes Page 31
F-Secure Plug-in for Cisco NAC Used by the Cisco Trust Agent, when checking the posture validation attributes of Anti-Virus Client Security Posture validation attributes are Virus definitions update status Real-time scanning protection status Firewall protection status Installed at the same time as CTA is installed Intelligent or policy based installation with PMC Page 32
Cisco Network Access Device (NAD) The NAD permits or denies network access Begins the client posture validation Typically a Cisco router Page 33
Cisco Access Control Server (ACS) ACS is responsible for obtaining and evaluating the posture validation attributes Determines the overall system posture Provides the appropriate network access policy to the NAD, based on the system posture ACS configuration example Healthy: Full network access granted Checkup: Outdated virus definitions usually no access restrictions Quarantine: Outdated virus definitions during outbreak access restrictions Unknown: No Cisco Trust Agent installed access restrictions Page 34
TROUBLESHOOTING
Typical Connection Problems Application Level (Application connection control) Application was by mistake denied from establishing connections Acting as client (e.g. Internet Explorer) Acting as server (e.g. nslookup) Firewall Level (NDIS Layer) Firewall blocks or allows all or certain connections Second Firewall is installed (e.g XP firewall, overblocking traffic) Firewall allows certain traffic, even though you have no specific allow rules Remember the Application Control dynamic rules Create specific static deny rules (or use pre-defined security levels) Page 36
Analyzing Internet Shield Problems Recommended ways to analyze Internet Shield problems are 1. Locally: Using the AVCS user interface 2. Remotely: Using Internet Shield web interface or console 2 1 Page 37
Local Troubleshooting Firewall Rules Static rules (outbound and inbound) Any rules blocking traffic? Any rules allowing unnecessary inbound traffic? Dynamic rules Any applications running, which allow unwanted inbound traffic? Page 38
Local Troubleshooting Firewall Settings Trusted Interface Make sure that this setting is locked (PMC Advanced interface) If adapters are trusted, all traffic passes unfiltered! Suspicious traffic alerting Don’t enable alerting of illegal packets (will create unnecessary alerts, increasing the size of your commdir) Can be used for debugging purposes on specific hosts Page 39
Local Troubleshooting Application Control Rules Application Connection Control list Listing all connection rules Separate row for server and client applications To avoid wrong user decisions, configure Application Control as follows First create a detailed application list (using test computers) After that, deny all new, unknown connections (client and server applications!) Page 40
Local Troubleshooting Main Logfiles Two main log files Action log; All firewall actions Packet log; All packets (header payload) Page 41
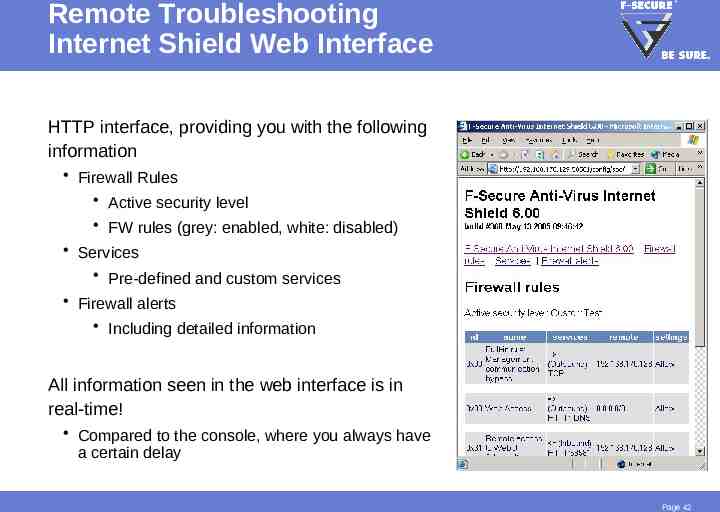
Remote Troubleshooting Internet Shield Web Interface HTTP interface, providing you with the following information Firewall Rules Active security level FW rules (grey: enabled, white: disabled) Services Pre-defined and custom services Firewall alerts Including detailed information All information seen in the web interface is in real-time! Compared to the console, where you always have a certain delay Page 42
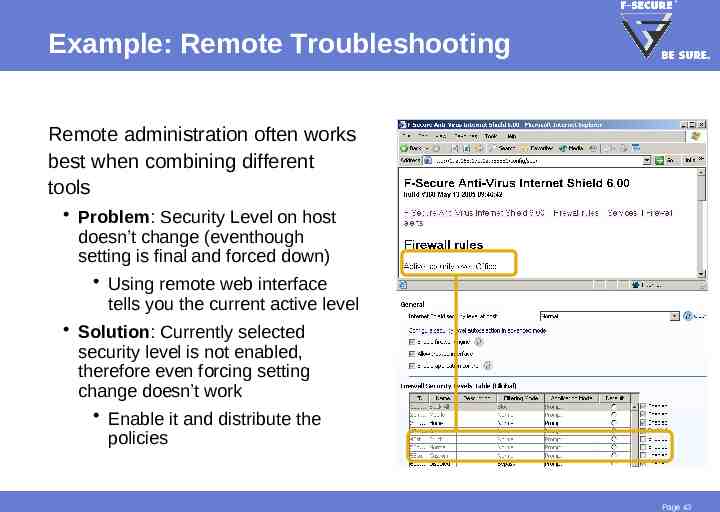
Example: Remote Troubleshooting Remote administration often works best when combining different tools Problem: Security Level on host doesn’t change (eventhough setting is final and forced down) Using remote web interface tells you the current active level Solution: Currently selected security level is not enabled, therefore even forcing setting change doesn’t work Enable it and distribute the policies Page 43
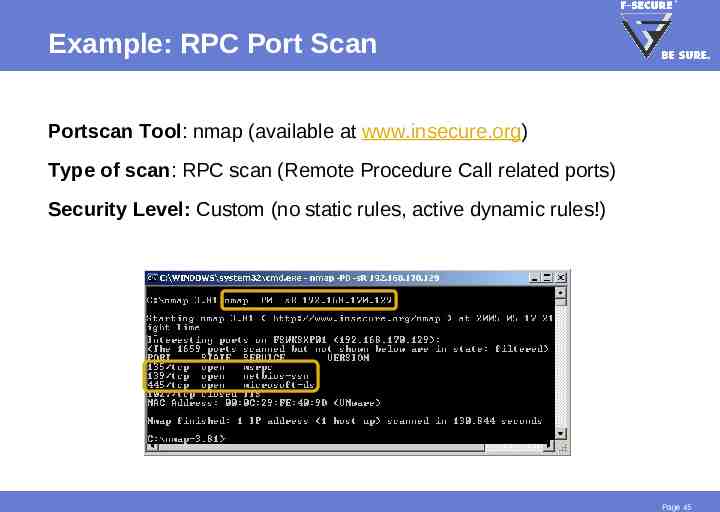
Testing Firewall Configurations Problem: You don’t know if the security level holds up against different kind of network attacks Select a host which currently has the security level in question active Run a full portscan (e.g. using nmap portscan tool) Only target that specific host Never run portscans in production networks! (unless you are responsible for the network) Page 44
Example: RPC Port Scan Portscan Tool: nmap (available at www.insecure.org) Type of scan: RPC scan (Remote Procedure Call related ports) Security Level: Custom (no static rules, active dynamic rules!) Page 45
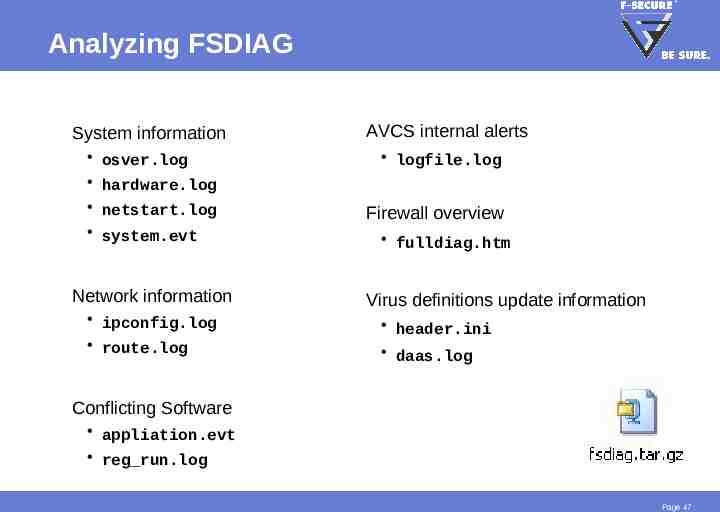
F-Secure Diagnostics Tool FSDIAG.EXE Diagnostics tool included in the installation package Collects important system information (eg. logfiles) to an archive on the local disk Access points C:\Program Files\F-Secure\Common\ fsdiag.exe Fsdiag.tar.gz in the same directory Page 46
Analyzing FSDIAG System information AVCS internal alerts osver.log hardware.log logfile.log netstart.log system.evt Firewall overview Network information ipconfig.log route.log fulldiag.htm Virus definitions update information header.ini daas.log Conflicting Software appliation.evt reg run.log Page 47
Summary Internet Shield Architecture Advanced functionality IDS vs. packet filter Stateful packet filters Dynamic firewall rules Cisco Network Admission Control (NAC) Troubleshooting Troubleshooting Internet Shield configurations Inspecting logfiles Page 48