A Survey of Trust Management Systems Speaker: Dalal Al-Arayed
32 Slides1.50 MB
A Survey of Trust Management Systems Speaker: Dalal Al-Arayed PhD-IT Student Supervised by: João Pedro Sousa, PhD Assistant Professor, CS, GMU
Outline What is Trust? What is Trust Management? Types of Models Main Problem Domains Trust Management Approaches Genealogy of Models Covered Description of Models Conclusion Evolution of Trust Management Models
What is Trust? Sociologist Diego Gambetta: Trust is a particular level of the subjective prob. with which an agent will perform a particular action, before [we] can monitor such action and in a context in which it affects [our] own action.
What is Trust? Cont. Trust is context-dependent, dynamic & non-monotonic. Types of Trust Interpersonal (agent & context specific Structural (system within which trust exists) Dispositional (independent of agent & context)
What is Trust Management ? “Trust Management” was first coined by Blaze et. al 1996 a coherent framework for the study of security policies, security credentials and trust relationships. Two of the first TM systems PolicyMaker and KeyNote.
Two Types of Models Trust Management models Certificate-based Reputation-based (behavior observed directly or indirectly) Recommendations: trust information shared among peers
Main Problem Domains Service Provision Blaze et.al (1996, 1998)- PolicyMaker & Keynote Abdul-Rahman & Hailes (2000) Aberer & Despotovic (2001) Capra (2004)- hTRUST McNamara et al.(2006) Quercia & Hailes (2006)-MATE Routing Buchegger et al. (2002)-CONFIDANT Cahill et al. (2003)-SECURE Quercia et al. (2006)-STRUDEL
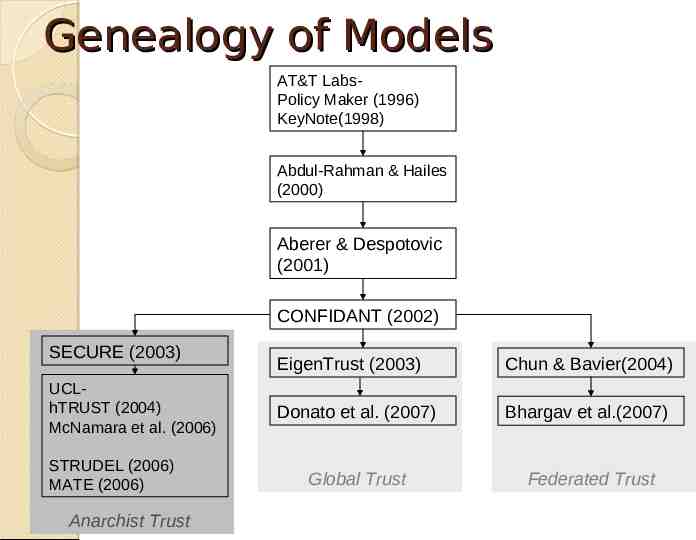
Trust Management Approaches Individual Initiative (Anarchist) each agent is responsible for his own fate. Global Trust each peer in the system has a unique global trust value that other peers can access. Federated Trust management of trust-related activities across multiple and heterogeneous security domains and autonomous systems. deals with strategies for managing interdomain behaviors
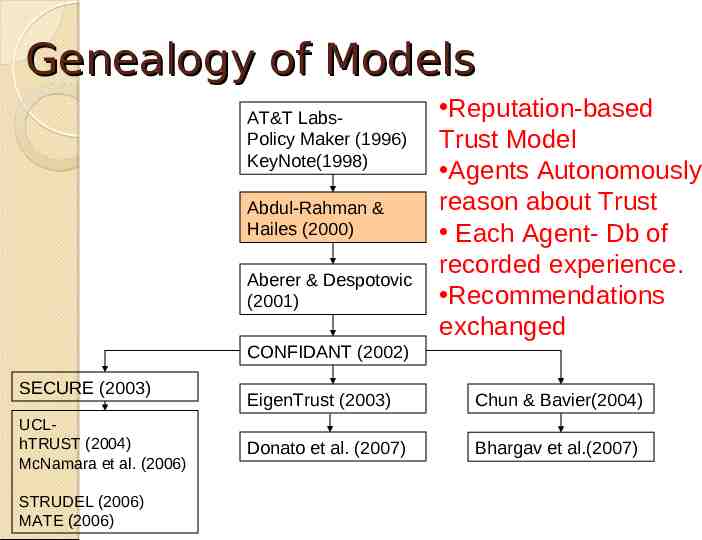
Genealogy of Models AT&T LabsPolicy Maker (1996) KeyNote(1998) Abdul-Rahman & Hailes (2000) Aberer & Despotovic (2001) CONFIDANT (2002) SECURE (2003) UCLhTRUST (2004) McNamara et al. (2006) STRUDEL (2006) MATE (2006) Anarchist Trust EigenTrust (2003) Chun & Bavier(2004) Donato et al. (2007) Bhargav et al.(2007) Global Trust Federated Trust
Genealogy of Models AT&T LabsPolicy Maker (1996) KeyNote(1998) Term: “Trust Management” PKI environments Certificate-based Trust Model Binds keys to actions Abdul-Rahman & Hailes (2000) Aberer & Despotovic (2001) CONFIDANT (2002) SECURE (2003) UCLhTRUST (2004) McNamara et al. (2006) STRUDEL (2006) MATE (2006) EigenTrust (2003) Chun & Bavier(2004) Donato et al. (2007) Bhargav et al.(2007)
PolicyMaker & Keynote (1996, 1998) Local policies, authenticated credentials, action string Application INPUT PolicyMaker OUTPUT yes/no or additional requirements for request to be acceptable Appears like a db query engine to the application. do not directly enforce policy; they only provide advice to the applications that call it.
Genealogy of Models AT&T LabsPolicy Maker (1996) KeyNote(1998) Abdul-Rahman & Hailes (2000) Aberer & Despotovic (2001) Reputation-based Trust Model Agents Autonomously reason about Trust Each Agent- Db of recorded experience. Recommendations exchanged CONFIDANT (2002) SECURE (2003) UCLhTRUST (2004) McNamara et al. (2006) STRUDEL (2006) MATE (2006) EigenTrust (2003) Chun & Bavier(2004) Donato et al. (2007) Bhargav et al.(2007)
Genealogy of Models AT&T LabsPolicy Maker (1996) KeyNote(1998) Abdul-Rahman & Hailes (2000) Aberer & Despotovic (2001) Reputation-based Trust Model Stored & shared data is exclusively negative(complaints) Distributed Storage CONFIDANT (2002) SECURE (2003) UCLhTRUST (2004) McNamara et al. (2006) STRUDEL (2006) MATE (2006) EigenTrust (2003) Chun & Bavier(2004) Donato et al. (2007) Bhargav et al.(2007)
Genealogy of Models AT&T LabsPolicy Maker (1996) KeyNote(1998) Abdul-Rahman & Hailes (2000) Aberer & Despotovic (2001) Detection & isolation of misbehaved nodes Neighborhood watch shared data is exclusively negative (warnings) Local storage of trust values CONFIDANT (2002) SECURE (2003) UCLhTRUST (2004) McNamara et al. (2006) STRUDEL (2006) MATE (2006) EigenTrust (2003) Chun & Bavier(2004) Donato et al. (2007) Bhargav et al.(2007)
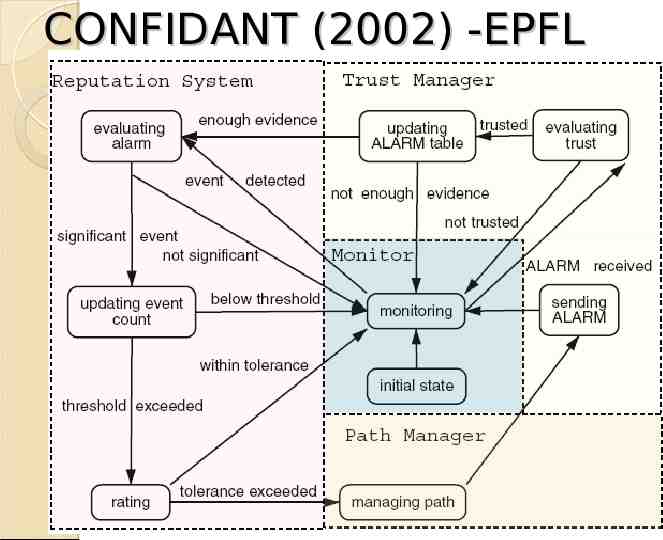
CONFIDANT (2002) -EPFL
Genealogy of Models AT&T LabsPolicy Maker (1996) KeyNote(1998) Abdul-Rahman & Hailes (2000) Aberer & Despotovic (2001) CONFIDANT (2002) SECURE (2003) UCLhTRUST (2004) McNamara et al. (2006) STRUDEL (2006) MATE (2006) Incorporates trust model & risk model Distinguishes between unknown and distrusted entities Enables delegation of trust evaluation Local storage of trust values EigenTrust (2003) Chun & Bavier(2004) Donato et al. (2007) Bhargav et al.(2007)
SECURE Project(2003)-EU
Genealogy of Models AT&T LabsPolicy Maker (1996) KeyNote(1998) Abdul-Rahman & Hailes (2000) Distributed trust models (Anarchist) Local storage of trust values Aberer & Despotovic (2001) CONFIDANT (2002) SECURE (2003) UCLhTRUST (2004) McNamara et al. (2006) STRUDEL (2006) MATE (2006) EigenTrust (2003) Chun & Bavier(2004) Donato et al. (2007) Bhargav et al.(2007)
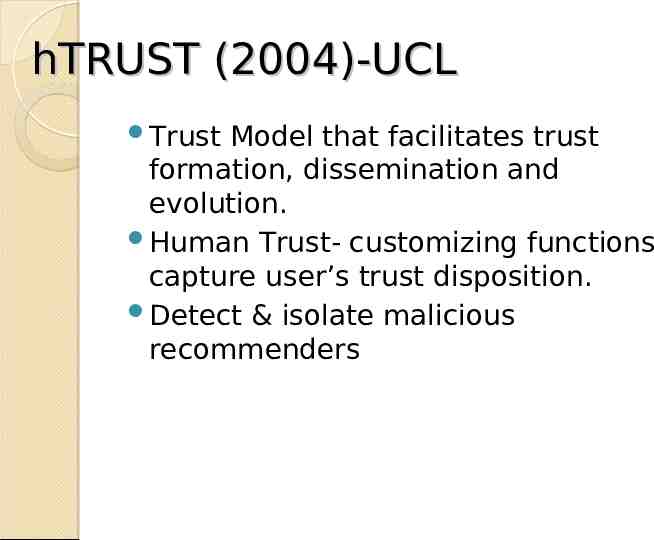
hTRUST (2004)-UCL Trust Model that facilitates trust formation, dissemination and evolution. Human Trust- customizing functions capture user’s trust disposition. Detect & isolate malicious recommenders
hTrust(2004)-Locally Stored Data Aggregate Trust Tuple Agent Trust Knowledg timeStamp e Tacit Tuples Recommend Trust er Portfolio of Credentials ( Recommend ed Knowledg timeStam e p ) Recommend Trus t SK recommender er t
hTRUST (2004)
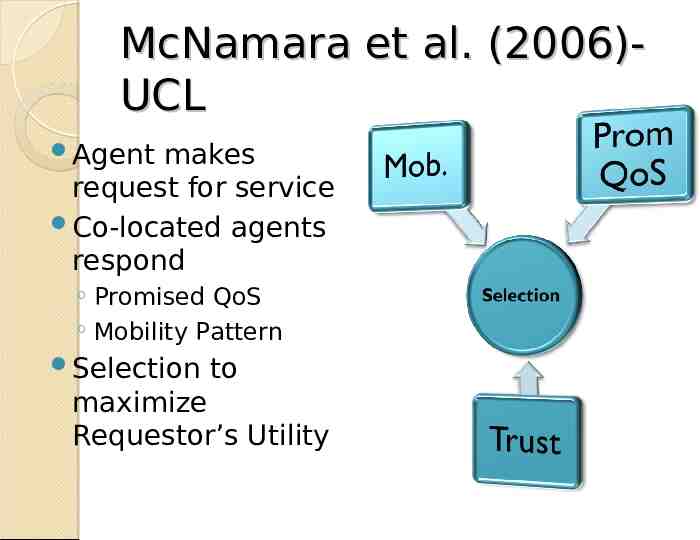
McNamara et al. (2006)UCL Trustworthiness – enables predictions about actual QoS given promised QoS Mobility introduced as parameter for decision making service requester and provider colocated for sufficient time to complete service delivery Mobility pattern: based on past journeys.
McNamara et al. (2006)UCL Agent makes request for service Co-located agents respond Promised QoS Mobility Pattern Selection to maximize Requestor’s Utility
STRUDEL (2006)- UCL Coalition Peering Domain Tragedy of the commons STRUDEL: distributed framework Approach for detecting malicious nodes based on the 2-ACK scheme Trust Model Forwarding mechanism (decision model).
STRUDEL(2006)- 2 ACK Scheme X Y Z If X does not receive ack from Y, Y is marked as unresponsive. If X does not receive ack from Z, Y is marked as suspicious Y did not send the packet to Z or Y relied on an untrustworthy peer Z.
MATE (2006)- UCL Attempts integrated mgt of trust & risk for decision making Expected utility theory incorporates trust info of sources, risk attitude of user, & context (location type) Risk restricted to timeliness of delivery.
MATE (2006)- Limitations risks scenario if component suppliers do not provide software within the agreed time ranges. Do not examine the potential risks from the way a software component actually operates. This situation might arise if the software component is signed with the author's key, thus guaranteeing the software integrity, and author is highly trusts.
Evolution of Trust Models Target Environ. Idea AT&T labs(1996, 1998) PKI A lot like Access Control AbdulRahman & Hailes (2000) Virtual comm. Intro to Reputation-based Trust Models & agents autonomy Aberer & Despotovic (2001) P2P Attempts distributed Storage of Trust info. CONFIDANT Mobile Ad(2002) hoc Attempts incorporation of Detection & isolation of misbehavior SECURE (2003) Attempts Incorporation of risk model with Trust Ubiquitous roaming entities
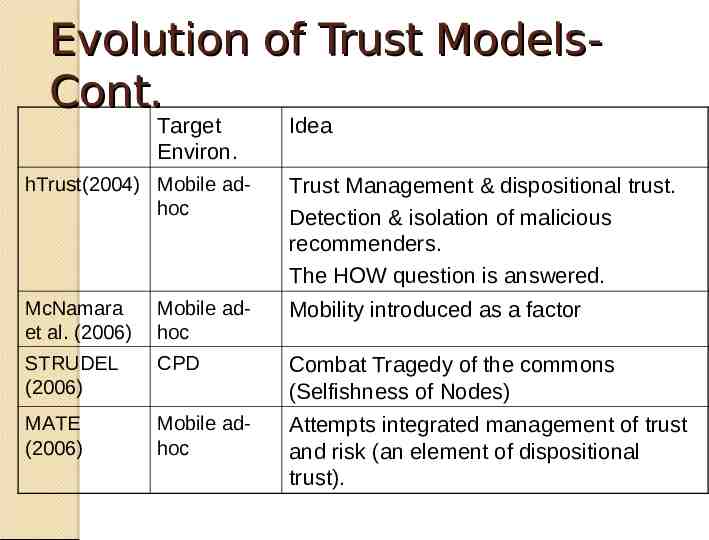
Evolution of Trust ModelsCont. Target Environ. Idea hTrust(2004) Mobile adhoc Trust Management & dispositional trust. Detection & isolation of malicious recommenders. The HOW question is answered. McNamara et al. (2006) Mobile adhoc Mobility introduced as a factor STRUDEL (2006) CPD Combat Tragedy of the commons (Selfishness of Nodes) MATE (2006) Mobile adhoc Attempts integrated management of trust and risk (an element of dispositional trust).
Questions?
References Abdul-Rahman, A. and Hailes, S. “Supporting Trust in Virtual Communities”. In Proceedings of the 33rd Hawaii International Conference on System Sciences, 2000. Aberer, K. and Despotovic, Z. “Managing Trust in a Peer-2-Peer Information System”. In Proceedings of the 10th ACM International Conference on Information and Knowledge Management, Atlanta, USA, November 2001. Bhargav-Spantzel, A., Squicciarini, A. and Bertino, E. “Trust Negotiation in Identity Management”. In IEEE Security and Privacy, volume 5, issue 2, pages 55—63, March 2007. Blaze, M., Feigenbaum, J. and Lacy, J. “Decentralized Trust Management”. In Proceedings of IEEE Symposium on Security and Privacy, pages 164--173, Oakland, CA, May 1996. Blaze, M., Feigenbaum, J. and Keromytis, A. “KeyNote: Trust Management for Public-Key Infrastructures”. In Proceedings of the 6th International Workshop on Security Protocols, volume 1550 of Lecture Notes in Computer Science, pages 59--63, Cambridge, UK, April 1998. Springer-Verlag. Blaze, M., Feigenbaum, J., Ioannidis, J. and Keromytis, A. “The KeyNote Trust Management System, Version 2. RFC-2704”. IETF, September 1999. Blaze, M., Feigenbaum, J., Ioannidis, J. and Keromytis, A. “The Role of Trust Management in Distributed Systems Security”. In Secure Internet Programming: Security Issues for Mobile and Distributed Objects, pages 185-210, 1999. Buchegger, S. and Le Boudec, J. “Performance Analysis of the CONFIDANT Protocol: Cooperation of Nodes — Fairness in Dynamic Ad-hoc Networks”. In Proceedings of IEEE/ACM Symposium on Mobile Ad Hoc Networking and Computing (MobiHOC), Lausanne, CH, June 2002.
References- Cont. Cahill, V., Gray, E., Seigneur, J., Jensen, C., Chen, Y., Shand, B., Dimmock, N., Twigg, A., Bacon, J., English, C., Wagealla, W., Terzis, S., Nixon,P., Serugendo, G., Bryce,C., Carbone, M., Krukow, K.and Nielsen, M. “Using Trust for Secure Collaboration in Uncertain Environments”. In IEEE Pervasive Computing Mobile and Ubiquitous Computing, volume 2, issue 3, pages 52-61, July-Sept. 2003. Capra, L. “Engineering human trust in mobile system collaborations”. In Proceedings of the 12th International Symposium on Foundations of Software Engineering, pages 107-116, Newport Beach, CA, USA, November 2004. ACM Press. Chun, B. and Bavier, A. “Decentralized Trust Management and Accountability in Federated Systems”. In Proceedings of the 37th Hawaii International Conference of System Sciences, Jan 2004. Donato,D., Paniccia, M., Selis, M., Castillo, C., Cortese, G. and Leonardi, S. “New metrics for reputation Management in P2P networks”. In Proceedings of the 3 rd International Workshop on Adversarial Information retrieval on the web, May 2007. ACM. Kamvar, S., Schlosser, M., Garcia-Molina, H. “The Eigentrust Algorithm for Reputation Management in P2P Networks.” In Proceedings of the 12th International Conference on WWW, New York, USA, ACM Press, pages 640--651, 2003. Mcnamara, L., Mascolo, C. and Capra, L. "Trust and Mobility aware Service Provision for Pervasive Computing". In Int. Workshop on Requirements and Solutions for Pervasive Software Infrastructures (co-located with Pervasive 2006), Dublin, Ireland, May 2006. Quercia, D., Lad, M., Hailes, S., Capra, L. and Bhatti, S. “STRUDEL: Supporting Trust in the Dynamic Establishment of peering coaLitions”. In Proceedings of the 21st ACM Symposium on Applied Computing, Dijon, France, April 2006. Quercia, D. and Hailes, S. “MATE: Mobility and Adaptation with Trust and Expectedutility”. International Journal Internet Technology and Secured Transactions (IJITST), volume 1, 2007.